Cybers Guards
on cyber security
- News
- Cyber Security
- Technology
- Reviews
- Content Delivery Networks
- Amazon CloudFront Reviews: Performance, Security & Real-World Insights
- BlazingCDN Review
- Akamai CDN Review: Performance, Security, and Pricing in 2025
- DNS (Domain Name System)
- Cloudflare CDN Reviews
- CacheFly CDN Reviews: Performance, Features, and Security Insights
- Fastly CDN Reviews: A Complete Guide for Businesses in 2025
- MaxCDN Reviews: Performance, Pricing, and Real-World Insights
- CDNsun Reviews
- Incapsula CDN Reviews
- KeyCDN Reviews
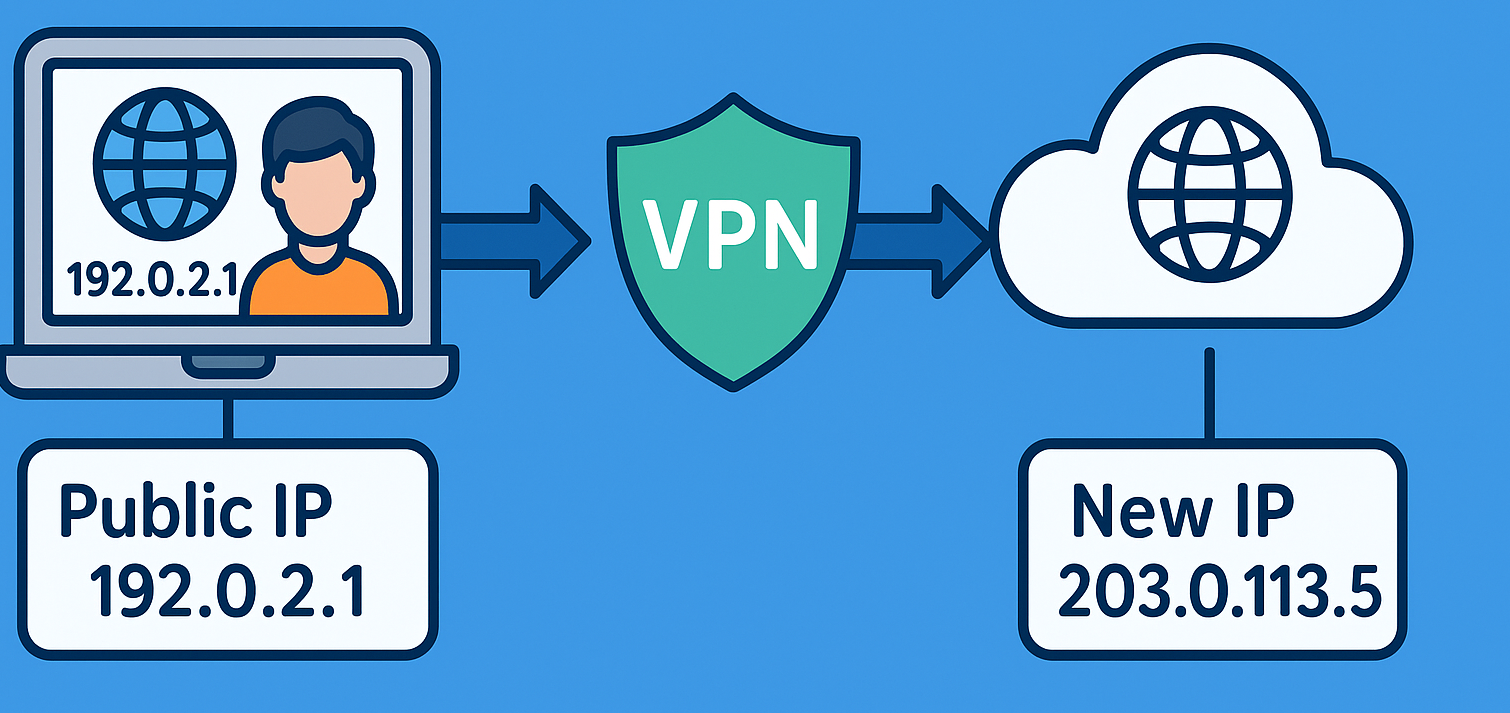
- VPN (Virtual Private Network)
- Content Delivery Networks
- Software
- Write For us
© Newspaper WordPress Theme by TagDiv