Simple steps to find Drupal Security vulnerabilities with below list of Security Scanning Tool Drupal is the third largest open source CMS with more than 4.5 percent market share.
Scanner for Drupal Vulnerability
More than 30 percent of Internet websites run on open source content management systems (CMSs) such as Drupal, WordPress and Joomla! CMS security becomes an increasingly important factor in the security of an organization.
Unfortunately, despite their popularity, thousands of Drupal installations contain vulnerabilities of high severity that could easily allow attackers to access the web server or even the underlying system in some cases.
With Drupal running a significant portion of websites on the Internet, it is no surprise that it is juicy targets for attackers-including novice attackers known as “script kiddies”-and CMSs. Some organizations may operate dozens of Drupal websites to add insult to the injury, making it a nightmare to track the security patches of each site they administer. There are nearly a million sites powered by them that attract an attacker and hacker more than enough.
If you use Drupal for your website and do not know if it is safe from known vulnerabilities, it does not display sensitive information, misconfiguration, etc., the following tools will help you.
Let’s list the tool that gives a better security results here.
1. Scanner by Hacker Target
A passive free drupal security scanner allows you to do low impact test for free of cost this includes
“Attempts to get CHANGELOG.txt and checks directory indexing. Also downloads the site main page and performs analysis on the HTML and HTTP Headers”
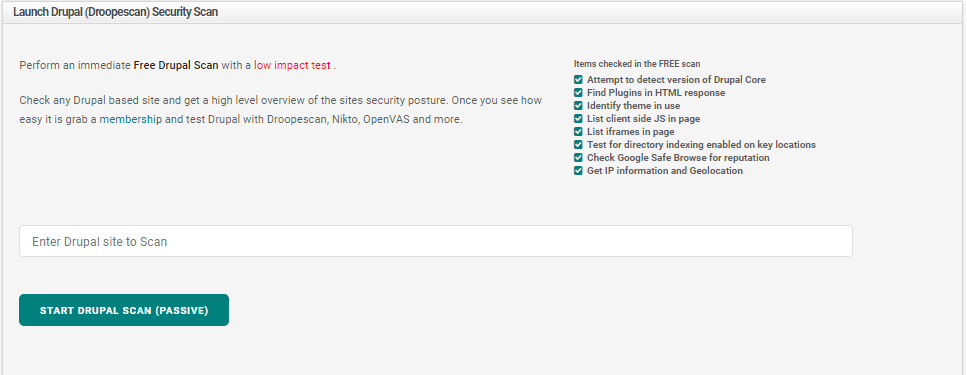
FREE scan hacker Target Checklist:
- Finding version of Drupal Core
- Find Plugins in HTML response
- Identify theme in use
- List client side JS in page
- List iframes in page
- Test for directory indexing enabled on key locations
- Check Google Safe Browse for reputation.
- Get IP information and Geolocation
Membership benefits
- Identify the attack surface by enumerating the extension and theme
- Access to 27 vulnerability scanners and OSINT tools
2. Droopescan
A plugin-based scanner that helps security researchers identify CMS problems. It is illegal to use droopescan to attack targets without prior mutual consent. It is the responsibility of the end user to comply with all applicable local, state and federal legislation.
Developers are not liable for any abuse or damage caused by this program. Please note that while droopescan outputs the most likely version of the CMS installed on the remote host, the user must manually perform any correlation between version numbers and vulnerabilities.
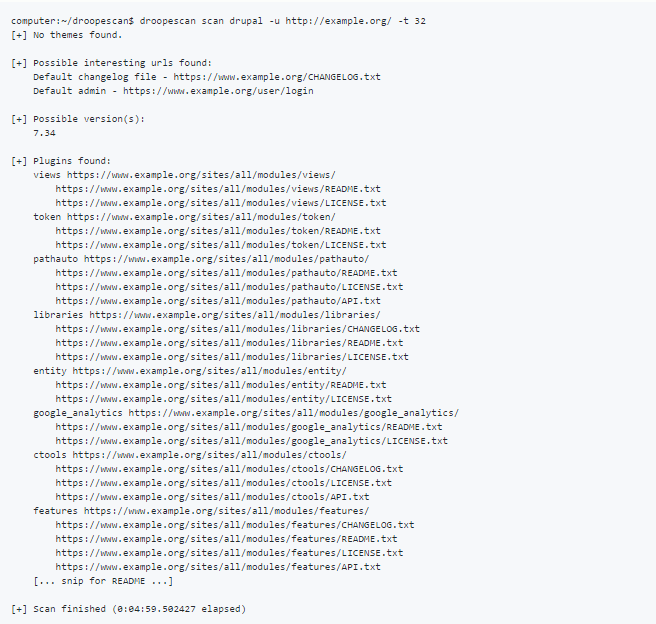
Droopescan mainly perform its scan on following path on your host server
- Plugins
- Themes
- Versions
- Sensitive URLs
3. Pentest Tools
Pentest Tools allows users to do security audit on durpal websites. This tool is also helps to identify the Drupal version, modules, themes and the current system configuration, the scanner performs a series of passive and active checks.
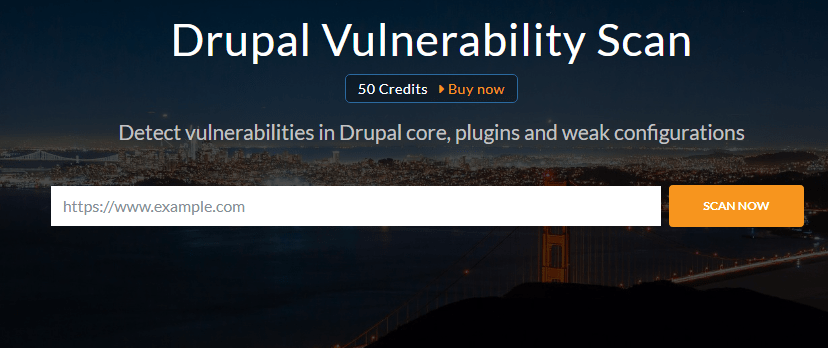
In addition, the core vulnerabilities of Drupal are removed from a local database that is regularly updated with the latest vulnerabilities affecting Drupal. The vulnerabilities are reported in the Drupal version identified.
Here are the most common drupal pentest performed by drupal vulnerability scanner.
- Search for vulnerabilities in the current version of Drupal
- Check the security of communication (HTTPS settings)
- Try to list the user using the Views module
- Check whether the login page is available
- Find the current theme of your Drupal version
- Find installed Drupal modules and more.
4. Acunetix
Acunetix is a web vulnerability scanner with a full – fledged Drupal security scanner designed to be easy – to – use, fast and dead while providing all the features necessary to manage and track vulnerabilities from discovery to resolution.
The Acunetix vulnerability scanner runs vulnerability tests in the core of Drupal.
Although Drupal modules can greatly expand a website’s capabilities, they usually display a larger attack surface, as they can be developed and distributed on the Internet by anyone and can therefore contain not only vulnerabilities, but also malicious code.
They offer a 14-day trial so try it out. You can select your scanner online so you don’t have to install anything on your server.
5. SUCURI SiteCheck
SUCURI SiteCheck is a general security scanner to quickly determine whether your Drupal site is infected with known malware, blacklisted and popular website error.
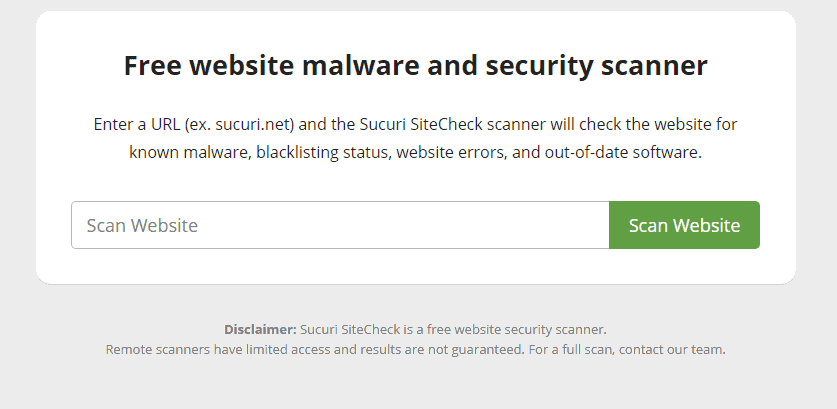
Nothing specific to Drupal, but any website should be scanned. SUCURI also provides Drupal sites with continuous security to protect and speed up.










Leave a Reply