A database comprising 6.840.339 distinctive StockX data breach user accounts is reported to be sold and circulated online. Bad competitors have already started decrypting the passwords and this data is anticipated to be used in future assaults.
It came to light last week that StockX was hacked and an intruder stole data from user accounts. This included usernames, email addresses, shoe size, shopping history and encoded passwords.
During the weekend, a data breach section has been introduced to your website by Pwned to enable customers to verify whether their emails are component of the infringement. This database, shared by the Dehashed.com password crush site, consists of 6,840,339 accounts containing “single e-mail addresses, names, physical addresses, purchases and passwords that have been saved as salted MD5 hash.”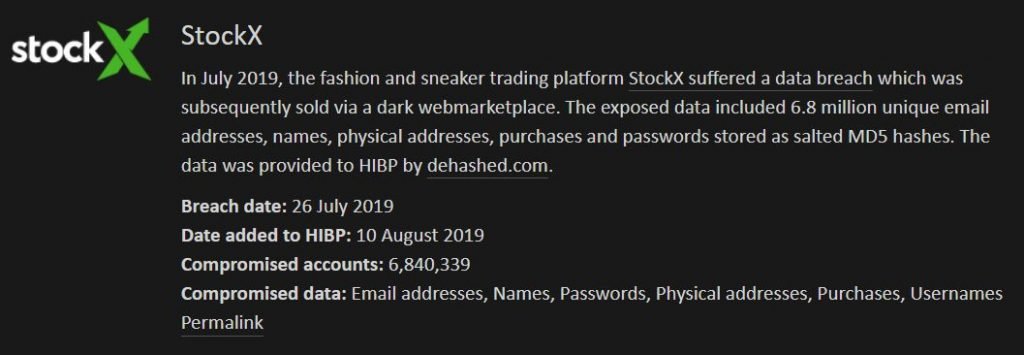
You can enter your e-mail address at https:/haveibeenpwned.com to verify if your data has been exposed as part of the violation and report if your data is in violation, including the StockX.
Database sold at hacker forums.
Security scientist Jim Scott, who helped HIBP with information dumping in the past, informed BleepingComputer that the StockX database was initially sold for $300 on the Apollon marketplace.
Since that time, the username and password combinations have been distributed for only $2.15 in underground hacker forums.
Since these rates mainly make the database free, it is now the hands of many attackers who are trying to break passwords.
For those who do not want to process password decryption, one person has supposedly decrypted 367,000 accounts and sold them for $400.
What should you do?
Now that the database dump is comparatively easy to use, the account credentials will be used for authentication.
A credential stuffing attack comes when attackers compile usernames and passwords that have been leaked from information violations of distinct companies and use these credentials to attempt to access other sites ‘ accounts. This sort of attack operates especially well with customers who use the same password on all sites.
If your password StockX is used on other sites, you should change your password immediately at all sites used. By not doing so, you risk compromising your accounts as well.











Leave a Reply