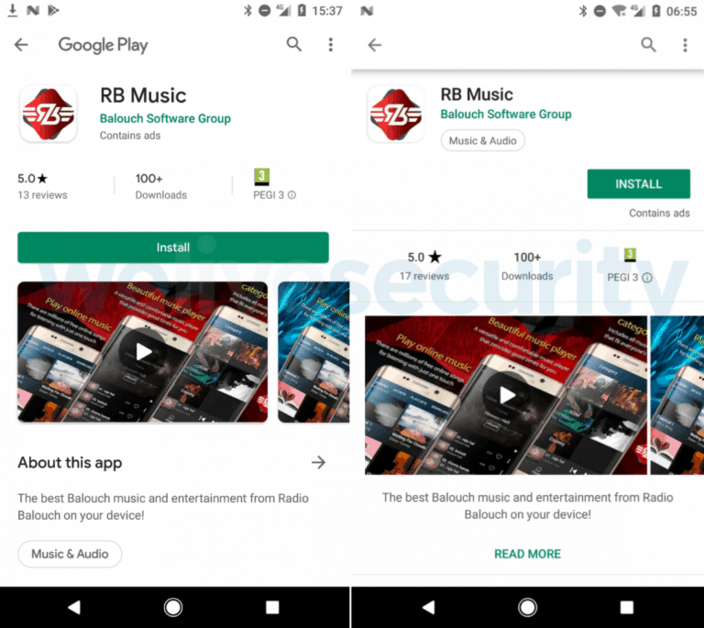
A spyware-based Android app based on an open source remote access tool (RAT) has twice damaged Google Play safety over two weeks.
Radio Balouch (or RB Music) includes the AhMyth Android RAT features, open source project software which was released by the end of 2017. Several malicious mobile applications have borrowed their code since its open release to spy on Android users.
For everything, there’s a first
Until now, there have been no reports of AhMyth applications that have been distributed globally via Google Play. That makes Radio Balouch the first to circumvent Google’s app screening system and turn it into the official Android app store.
It is fully functional to stream music from Balouchi, the traditional Balochistan region of southwest Asia and to steal contacts, to harvest files and to send SMS messages. RB Music is also completely functional.
The SMS function nevertheless doesn’t operate, because of latest Google Play checks requiring an app “to be actively registered as the default SMS or Assistant Manager on the device.” ESET malware researcher Lukas Stefanko claims the spyware based on AhMyth is accessible in other app shops and is promoted on YouTube and Instagram. No response was received despite reporting the campaigns to the service suppliers.
First reported on Google Play on July 2nd, the malicious Radio Balouch app was deleted a day later. On July 13th a comeback was discovered and Google started it rapidly. The number of downloads was higher than 100 in both cases.
Research by ESET does not mention any unique steps to go beyond Google’s safety checks, all the more surprising because AhMyth is accessible for so long and has no flawed code.
While 100 downloads are not very distributed, it should be noted that following the ESET report, the spying app was kicked off from the official Android shop.
Better screening is necessary
Spying-ready versions of RB Music remain in third-party app shops, Stefanko says, and the developer is most likely to begin promoting Instagram and YouTube accounts.
“The attackers’ Instagram account still, at the time of writing, serves a link to the app that has been removed from Google Play. They have also set up a YouTube channel with one video introducing the app; apparently, they don’t promote it as the video has a mere 21 views at the time of writing.”
Research from ESET demonstrates that Radio Balouch provides the choice of registering an account. This is only an appeal to the user to type login credentials, because any input indicates that the procedure has been effective.
Stefanko thinks that this feature is used to harvest logins to test them in credential assaults from other facilities.
The investigator warns that clones of this app or AhMyth derivatives can appear in the Play Store unless Google increases screening for malicious applications.
“While the key security imperative “Stick with official sources of apps” still holds, it alone can’t guarantee security. It is highly recommended that users scrutinize every app they intend to install on their devices and use a reputable mobile security solution.” – Lukas Stefanko










Leave a Reply