A Microsoft Remote Desktop Protocol (RDP) vulnerability may also be used to escape virtual Hyper-V virtual machines, Azure virtualization technology and Windows 10.
The bug is a remote implementation route that was reported to Microsoft almost a year ago as having only an effect on RDP and was unpatched until recently, when it was found that it had an influence on the Hyper-V product in Microsoft.
Microsoft initially validated the finding but rejected a fix that “did not fulfill our service bar.”
Eyal Itkin of Check Point released the technical information of the error in February as part of a major study covering several RDP vulnerabilities. He focused on the inverse RDP attack in which a remote server gains control of the client.
This was because two RDP connected machines share the clipboard, so everything copied on the remote server can be pasted onto the local client.
RDP in virtual Hyper-V computers
There is an immediate link between virtualization and remote desktop technology, but Hyper-V depends on Hyper-V to enhance its functionality.
However, Hyper-V improved session mode allows an RDP connection to virtual machines. The instruments and files are shared between the two systems.
With enhanced session mode active, the relationship between the two products is apparent because both a virtual Hyper-V computer and a remote link via Microsoft’s RDP customer (mstsc. Exe) have the same settings window.
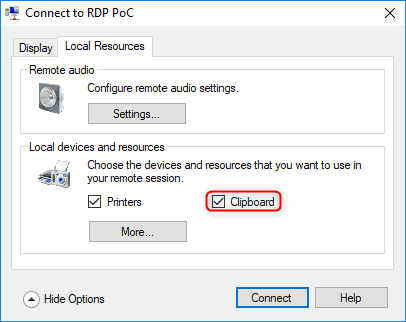
It also synchronizes the content of the clipboard and is enabled by default. Itkin used the same proof-of-concept script for the Hyper-V context that showed RDP fault and worked the same way.
In this situation, however, the investigator has accomplished a virtual escape guest-to-host. The video on the PoC below demonstrates how the attacker can add a malicious file into the Host Startup directory by merely pasting a host-connected file to a malicious virtual machine, ensuring implementation on the next boot.
Itkin informed BleepingComputer that a vulnerability could be used by an attacker to compromise computers of privileged business customers. By forcing an administrator under their command to link to a desktop or virtual machine, an opponent can escalate the assault.
“Once someone connects to the computer using RDP, the attack starts. If the victim, the connecting client, issues a “paste” operation while the connection is open, even pasting on his computer, they are vulnerable. The attacker could use a vulnerability in the shared clipboard to drop arbitrary files to arbitrary locations on the target’s computer, effectively taking over it.” – Eyal Itkin
Presented with fresh results, Microsoft has altered its original position and released a vulnerability identification number (CVE-2019-0887) and July safety updates patch.
“While it was hard for any security researcher to miss Microsoft’s effort to test and improve the security of its Hyper-V technology, we can learn an important lesson from this research. As the saying goes: your system is only as strong as its weakest link. In other words, by depending on other software libraries, Hyper-V Manager inherits all of the security vulnerability that are found in RDP, and in any other software library that it uses.”
If only subsequent updates can be installed, the investigator claims the default disabling of the shared clipboard will neutralize the vulnerability.
Information on the attack and its inherent flaw is provided at the Black Hat US Security Conference where Itkin and Dana Baril, Microsoft’s safety software engineer, both speak from a defender’s point of view.
In an article titled “Case Study in Industrial Collaboration: Poisoned RDP vulnerability disclosure and reaction,” Microsoft wrote on this vulnerability.
The following declaration was also given to BleepingComputer:
“A security update was released in July. Customers who apply the update, or have automatic updates enabled, will be protected. We continue to encourage customers to turn on automatic updates to help ensure they are protected.”











Leave a Reply