In Microsoft’s attempts to infect individuals with malware, gather sensitive information or trick them into making fraudulent payment, the client warned of the dangers behind the phishing attacks by threatening actors.
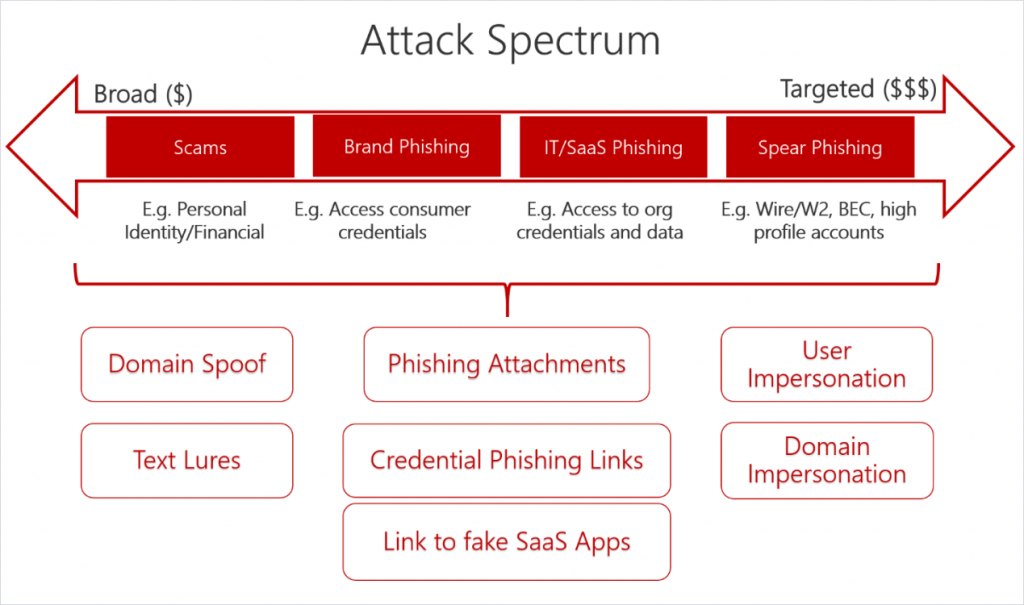
Although standard phishing campaigns do not pick up and use a shootgun spray approach in order to compromise as many objectives as possible effectively, spear phishing attacks use personalized messages for one single objective.
“In fact, they are so targeted that sometimes we call them’ laser’ phishing,” says Microsoft. “And even technical managers and other top managers have been tricked into handing over money and confidential documents via a well-targeted email because these attacks are so focussed.”
Diana Kelley, Cybersecurity Field CTO of Redmond, and Seema Kathuria, Senior Manager, Cybersecurity Solutions Group, emphasize how hackers plan and carry out spear phishing attacks.
Thus, menacing players who carry out such campaigns would first carry out recognition tasks in order to identify potential objectives within an organization and to send them to initiate and later think about possible victims.
When the spear phishing attack succeeds and the victim baites, the attackers can obtain information or perform a variety of malicious activities after the victim’s system is infected with malware.
Depending on the number of victims targeted by a phishing campaign, the payout is dramatically increasing and most threats are able to get more money for their efforts when they concentrate on fewer or even a single carefully chosen victim.
Microsoft says that companies and their employees can take measures that could greatly reduce risks when it comes to detecting spear phishing attacks and blocking them.
Organizations can use learning to educate their employees to identify and plan phishing messages for signs of e-mails such as:
• sender addresses that don’t match with the sender’s identity
• language designed to induce a sense of urgency
• requests to break established procedures
• wording inconsistent with the company’s usual terminology
On the other hand, workers who might be targeted in such campaigns should be encouraged to interact with others in the organization when they receive a suspicious email and to warn the security team when they do so, ensuring that everyone is alerted to them.
Last but not least, multi-factor authentication (MFA) prevents spear phishers from controlling other company resources, effectively limiting the damage an intruders could cause, once the victim’s system or account is compromised, and maintaining persistence within the network of an organization.
In July, a large-scale spear-phishing attack sequence targeting around 100 orgs with malspam-emails spreading malware to LokiBot data robber was discovered by the Defender ATP Research team of Microsoft.
The company is also introducing an improved phishing messages notification system for administrators in all Microsoft 365 environments as well as a new’ Unverified Sender ‘ feature designed to make phishing emails sent to its clients simpler for users.











Leave a Reply