Microsoft is currently developing significantly improved Office 365 Threat Explorer manual threat hunting features which will be implemented in all environments throughout August.
Office 365 is one offered by the Microsoft 365 software package that also includes two more offers, Windows 10 and EMS (Enterprise Mobility + Security shortcuts).
Threat Explorer is an Office 365 ATP (Advanced Threat Protection) customer safety & compliance Center tool that enables Security Operations teams to review and respond to threats such as malware and phishing in their inboxes, emails and malicious data.
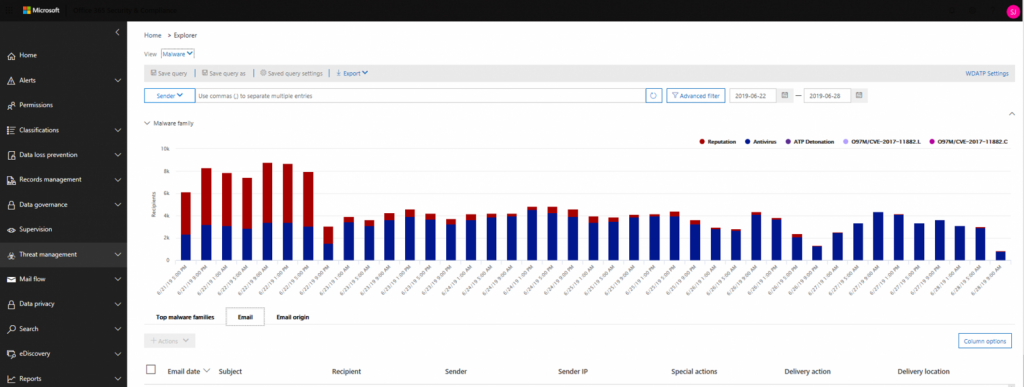
Threat Explorer
Threat Explorer hunting enhancements
In the beginning, Office 365 admins with access to Threat Explorer may preview and download malicious emails for further analysis, which will make it much easier to analyze bad emails.
Secondly, an email timeline for differentiating several events triggered by the same malicious email will be available as part of Office 365 Threat Explorer.
This allows the hunting process to be simplified and efforts focused on several points of interest to avoid wasting time on the same malicious message.
Last but not least, emails are also given a pair of columns showing their current delivery status, with’ Delivery Action’ to display whether the message is delivered, sent to junk, blocked, or replaced by ZAP and’ Delivery Position,’ to specify the exact location of the email.
“Events that may occur after the delivery of an e-mail are captured under the column” Special Action. “All these combined values would help the admin to understand what action(s) were done in an e-mail and where the e-mail was located,” added Microsoft on the Microsoft 365 roadmap update.
Microsoft offers detailed instructions for how to use
Threat Explorer and real-time detection to detect and analysis malicious contents, both in files and in emails with instructions on viewing URLs, reviewing user-reported emails and how to launch automated surveys to save time.
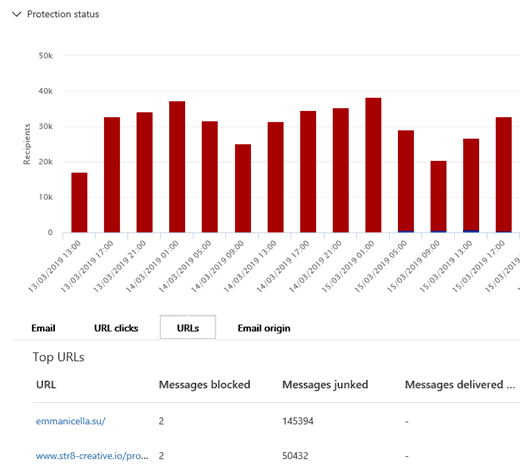
Threat Explorer phishing email report
Redmond announced yesterday in related news that changes to simplify Office 365 licensing technology for Office-based subscription customers will also be made next month..
Last week, the new Office 365 group user activity expiration policy, now available for selected Azure AD Premium customers and aimed at automated lifetime renewals without any user intervention requirements, was also released in private preview.
The new expiry policy for Office 365 groups helps all Microsoft 365 administrators improve the management of the life cycle group after the feature is released for the general public and active groups are automatically renewed once their lives expire.










Leave a Reply