In six applications, the spyware has spread to 196 different countries.
An Android spyware dubbed MobSTSPY has enabled Trojan-based apps to be distributed globally, mainly via Google Play.
Malware masquerades as a legitimate application that claims to be torches, games and tools for productivity. While it is not uncommon to find armed goods in third – party app stores, MobSTSPY has also managed to infiltrate Google Play with at least six different apps in 2018.
“Parts of what makes this case interesting are the widespread distribution of its applications,” said Trend Micro researchers Ecular Xu and Grey Guo on Thursday. “Through our back – end monitoring and in-depth research, we saw the overall distribution of affected users and found that they came from a total of 196 different countries.”
These range from Mozambique to Poland, Iran to Vietnam, Algeria to Thailand, and Germany to Iraq and so on.
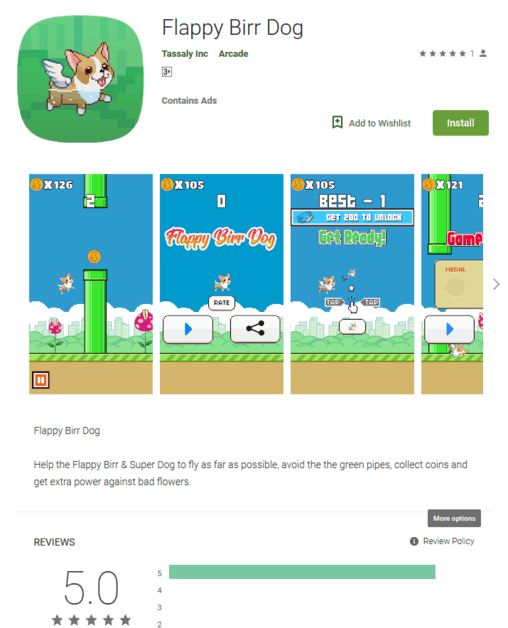
The Google Play apps were Flappy Birr Dog, FlashLight, HZPermis Pro Arabe, Win7imulator, Win7Launcher and Flappy Bird, all of which came out of the store last year. Some of them have been downloaded more than 100,000 times from users around the world.
The bad code is primarily an information stealer in terms of capacity, although it also has a unique phishing aspect. When it comes to the former, it removes data such as user location, text messages, contact lists, call logs and clipboard items and can steal and upload files on the device. Trend Micro noted that it uses Firebase Cloud Messaging (FCM) to communicate with its C&C server and that it scans data according to the command it receives.
It also collects at the beginning useful device information, such as the language used, its registered country, package name, device manufacturer and so on, which can be used to ” fingerprint ” the device for social engineering follow – up or exploit attacks. ” It sends the information collected to its C&C server and therefore registers the device, “said the researchers.”
Once done, malware will wait and execute commands sent via FCM from its C&C server. “In addition to its info-stealing capabilities, malware can also gather additional phishing credentials. It displays fake Facebook and Google pop – ups requesting account details for the user; when entered, it returns a “unsuccessful login ” message that may not raise a red flag for the user.
“[ The MobSTSPY case] shows that while apps are prevalent and useful, users must remain cautious when downloading them to their devices, ” the Trend Micro researchers noted. ” The popularity of apps serves as an incentive for cyber-criminals to continue developing campaigns that use them to steal information or carry out other types of attacks. ”
Google Play Malware
Google Play malware is relatively rare, but this is certainly not the first time that Google Play filters and policies have been evaded. In November, a booby – trapped Android app called the Simple Call Recorder was downloaded–after almost a year of downloading. The main purpose of the malware was to make the user install another app that was supposed to be an Adobe Flash Player Update. In addition, early last year, Google removed 22 malicious adware apps from flashlights, call recorders, and WiFi signal boosters that were downloaded from the Google Play marketplace up to 7.5 million times.

And in 2017 Google launched 700,000 Google Play apps to violate market policy. These were not all malware, but mostly copied a more popular app or served inappropriate content.
The problem is, of course, that when malicious applications are deleted, people who already have them on their smartphones are not notified of the problem –so millions of users still have different malware installed on their devices. In fact, a study carried out by the Pradeo Lab in November 2018 showed that 89% of malicious applications deleted from stores are still installed on active devices six months after they have been deleted.











Leave a Reply