Maltego is an intelligence gathering tool, its available for windows, mac, and Linux. We will be using Kali Linux where it’s available by default. Remember to register on their website and I have it setup.
There are a lot of things maltego can do not just information gathering it can also brute force a website login page, SQL injection and testing the targets. Now we will be looking at how to do a fast Vulnerability test on a website using maltego. Get to know about free online sql injection scanner here.
Open a terminal and type “maltegoce”. You should have it up and be running, register and make sure you give a legit email I d since they will be sending confirmation links etc.. Now it will ask you to start a machine.
Installing Maltego Teeth
Open terminal and type in “apt-get install maltego-teeth“.
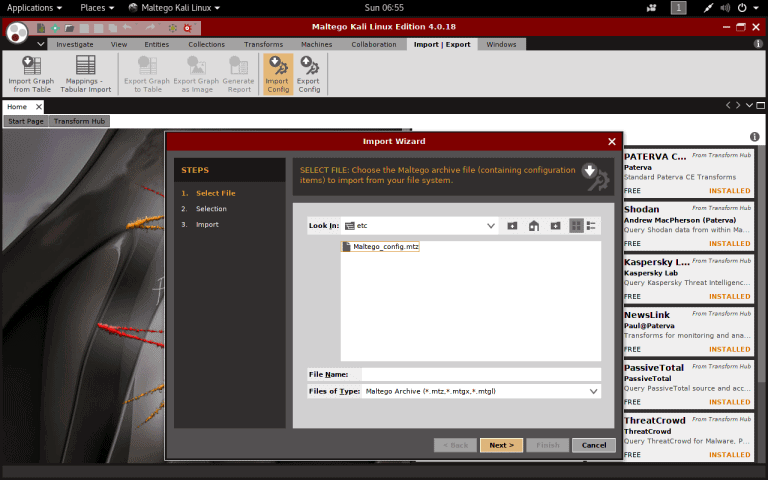
Upon downloading maltego teeth, we will have to import the configuration file from the following folder/opt / Teeth / etc / Maltego config.mtz.
select all the entities and click next and finish.
Click Ctrl + t. In front of you, you will have a blank graph open. You will see a lot of entities like banners, port, website etc on your left. Drag the web-site-entity into the empty diagram and type into the website you like.
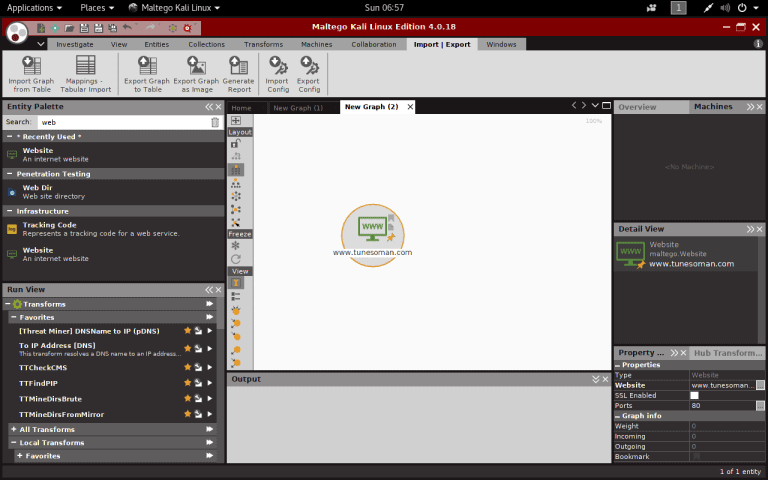
Now let’s try to get the IP address via reverse DNS to IP. Scroll down the run view to find “To IP Address [DNS]”.
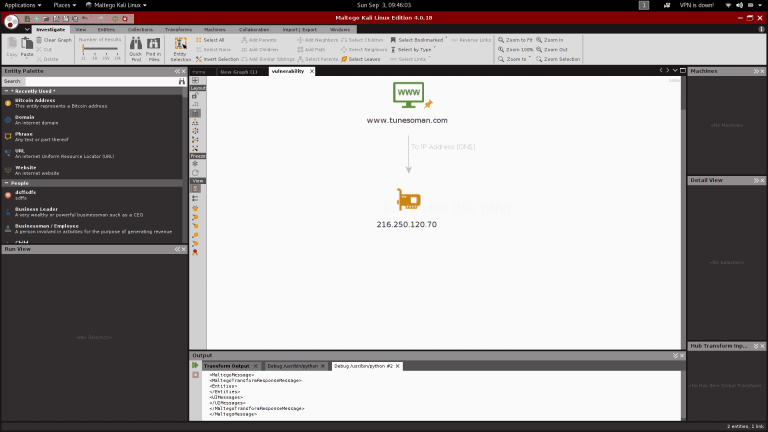
Then click on the IP Address (“TTNMAPPLUS”) and on the local transform button, to the left, press the “TTNMAPPLUS” button, it takes a minute or two depending on your Internet connection speed to get the answer.
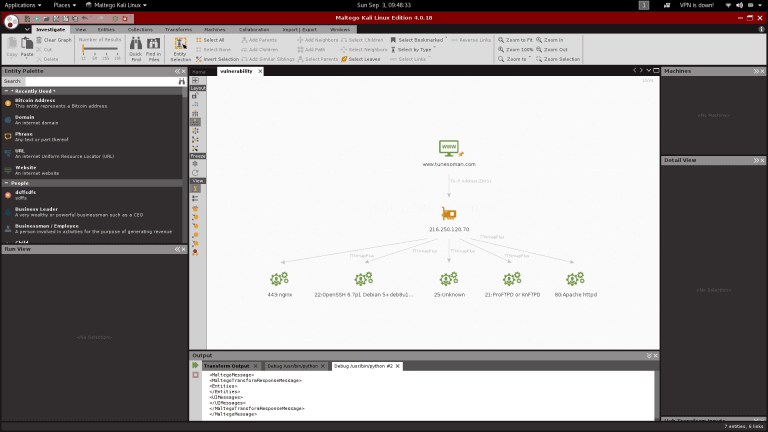
Now select all ports, banner capture and view certain ports services using “T TTserviceetoPort” and “TTServiceToBanner.”
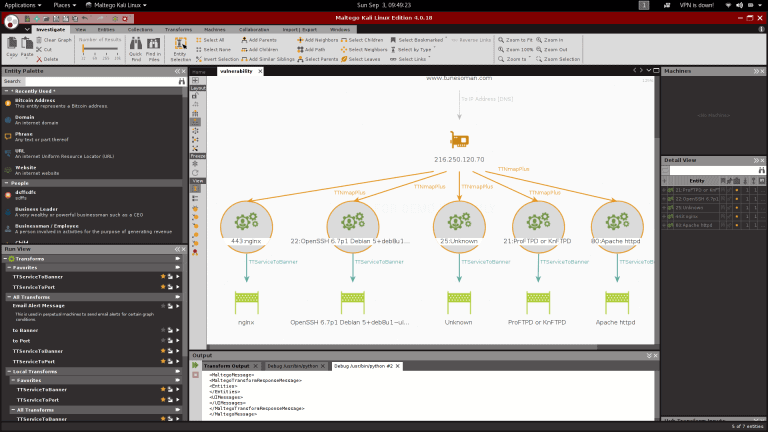
Then we can search quickly with” TTquickVulnSearch “to see whether maltego selects anything that’s juicy.

Maltégo finds that the web server has a Debian 5 database that is really old and prone to many vulnerabilities. It also indicates what types of vulnerabilities are identified in the right-hand view.











Leave a Reply