After a series of successful supply-chain attacks, two popular games and a games platform developed by Asian companies have been compromised which have allowed attackers to include a malicious payload to provide a behinddoor.
The software used for the attacks on the supply chain is designed to check the region of the machines affected before the payload drops and, if the computer is Chinese or Russian, it will automatically stop the infection process, showing that the cyber criminals behind the attack have a very particular list of victims that they have to target.
The affected executable will start the malware payload on a affected system before other components, decrypting and memory-launching the backdoor in advance or using the game or gaming platform code.
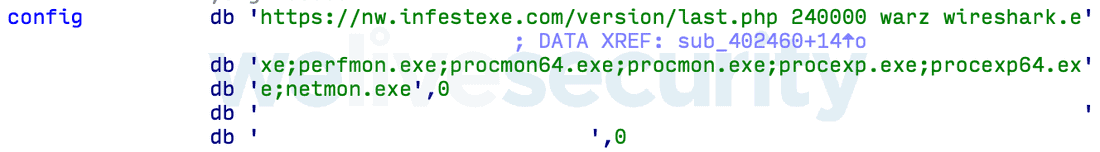
During analysis, ESET identified five versions of wild malicious payload using similar configuration files, including the Command-and-Control (C&C) Server URL, a pre-configured wait time to latency execution, a string containing the campaign name, and above all a list of executable to be shut down if the backdoor is running on the infected system.
If the backdoor doesn’t shut down after checking for anti-malware solutions, the backdoor will generate a bot identification which it packs together with’ user name, computer name, windows version, and system language.
While three of the four commands support the backdoor— DownUrlFile, DownRunUrlFile, RunUrlBinInMem— it is actually disabled by setting the HKCU\SOFTWARE\Microsoft\Windows\CurrentVersions\ImageFlag registry to 1.
Install will disable the fourth command called UnInstall. As the ESET researchers say: “When payloading begins, the registries are requested and execution is aborted if set. Maybe attackers try to reduce the load from their C&C servers by avoiding uninteresting victim callbacks.”
While the malware also comes with a second-stage payload that installs itself as a Windows service and is intended to auto-update itself, its exact functionality In ESET’s Marc-Etienne M. Léveillé analysis the malware used in the supply chain attacks on the developers of the game is the same, but the threat actors used different configurations for each attack.
Despite the different approach, the backdoor of the affected software products in all three cases was the same. Given the popularity of the hacked playing platform and games in Thailand, the Republic of the Philippines and Taiwan–the 3 most hit countries–the ESET researcher concluded after analysis of the telemetry data collected during the analysis is likely to number tens or even hundreds of thousands.

At the end of ESET’s analysis, there is a comprehensive collection of compromise indicators (IOCs) containing compromised file samples, payload samples, second stage samples and MITRE ATT&CK Matrix.
Successful supply-chain attacks have led to hundreds of millions of damage
With supply-chain attacks increasing by around 78 percent during 2018 as reported in the 2019 Internet Security Risk Report.
In January, hundreds of e-commerce sites were affected by a MageCart attack, which compromised a French online advertiser Adverline advertisement script.
While Magecart attacks were widely reported in 2018, with large companies including British Airways, TicketMaster, OXO and Newegg affected, the number of victims can compromise huge numbers of victims when the supply chain attacks are involved too.

In 2018, hackers succeeded in compromising several organizations ‘ supply chain in South Korea, inserting malware into 141 Android devices with low-cost costs and infecting 400,000 users after successfully backdooring the Russian MediaGet BitTorrent customer.
Threatening actors had used the same methods a year earlier as part of the NotPetya attack, which led to hundreds of millions of US dollars of damage, the ShadowPad attack with a backdoor on multi-financial institutions ‘ server management software and infect the CCleaner tool which landed on their users ‘ computers.











Leave a Reply