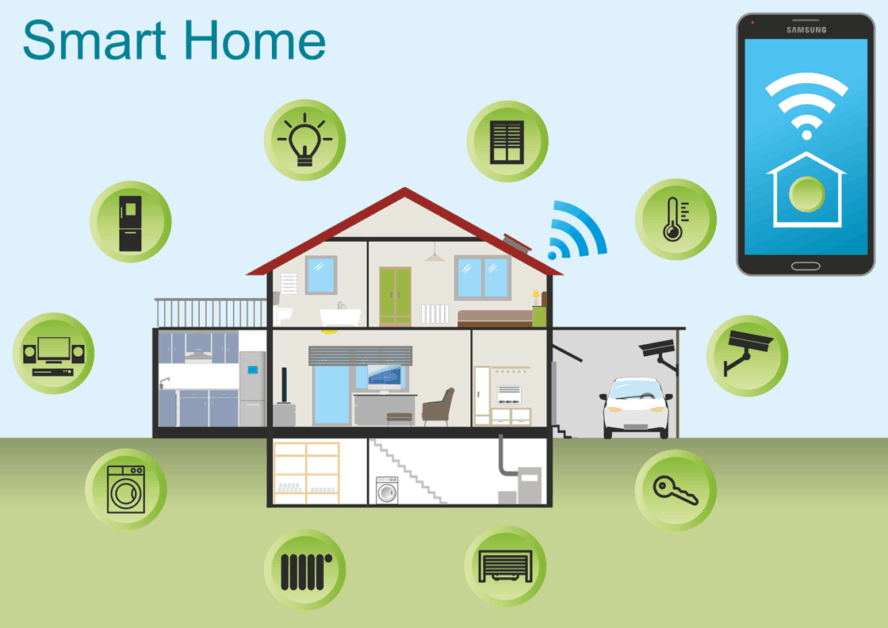
KeyWe smart locks vulnerability could be exploited to intercept key and unlock doors by attackers. An intelligent house is a fragile home. It has a large number of interconnected IoT devices and is linked to the internet via a router that probably has the same, unchanged, default password. Sometimes the connection is via a mobile phone request, sometimes causing additional weakness.
These have a different characteristic at this stage in the evolution of intelligent homes: by nature, these are the residence of rich or important people. It makes the intelligent home a destination for cyber criminals and–probably –a target for the physically competent cyber burglar. The latter is not yet a major vector of crime, but is likely to increase.
The latest discovery from F-Secure of a design fault in an intelligent lock illustrates the hazards. The brand is the KeyWe Smart Lock, a remotely controlled entry system used mostly in private homes. On your mobile phones, users can open and close doors via an app.
The fault is not in the lock, but between the device and the door. The lock is quite secure and requires data encryption to prevent unauthorized parties from accessing critical information about the device, such as a hidden passphrase. Contact between the lock and the control app is not so safe. This uses Bluetooth Low Energy over WiFi and although it is obviously encrypted, the layout is faulty: between executions the standard key doesn’t change, but with the devices address it does.
“This is a serious mistake!” says Krzysztof Marciniak of F-Secure Consulting in a related post. “Because an in-house key switch-with only two values involved-is used for decrypting all correspondence, the transmission needs to be stopped, and the specific key can then be determined easily on the basis of the phone address.” He says,’ Sadly,’ the lock’s design makes it rather simple for hackers to circumvent such mechanisms to wake messages from the lock exchanged and the app-leaving them alone. There is no way to mitigate it, so it is a safe bet for burglars who can duplicate the hack to get into the locked houses. What attackers need a little know-how, a tool to help them catch traffic, which can only be purchased from many consumer electronic stores for as little as 10 dollars, and a little time to find the lockers.’
A sniffing system could be concealed by the door awaiting homeowner’s return. That’s not easy, but when IoT Device Sellers go on the ship with goods that cannot receive an upgrade, it is critical that these devices are designed in order to make them secure from the ground up. “F-Secure mentioned this problem to the vendor who was receptive in contact with researchers. According to the manufacturer, a security patch will be issued for new devices. The next version of the lock will also have a firmware upgrade feature–but no information on the date of release is available. “Secure design is a principle that is still not used by all manufacturers of intelligent devices. In this instance, security in the lock, but not in the environment, in which it is being used, is designed.










Leave a Reply