In an era where online anonymity and privacy are prized commodities, tools like 911 proxy VPN have grown in popularity among cybersecurity professionals, privacy enthusiasts, and even industry leaders. But what exactly is 911 proxy VPN? How does it differ from traditional VPNs or proxies? And what are the associated benefits and risks in 2025’s digital landscape?
This comprehensive guide answers these questions by exploring the origins, functionality, usage, and controversies surrounding 911 proxy VPN services. It also guides users on safer alternatives and practical applications to protect privacy while staying compliant and secure online.
What Is 911 Proxy VPN?
The term “911 proxy” originated from 911.re, previously one of the largest residential proxy services globally, known for offering access to a vast pool of rotating residential IP addresses. While primarily a proxy provider, it’s often combined with VPN features, leading to the term “911 proxy VPN.”
-
911 Proxy VPN works by routing a user’s traffic through residential IPs rented or sourced from real users’ devices worldwide.
-
It provides anonymity by hiding the user’s real IP address behind residential proxies, making traffic appear as originating from normal home devices.
-
Often used for web scraping, geo-unblocking, ad verification, and market research.
How Does 911 Proxy VPN Work?
The Network and IP Rotation
911 proxy VPN leverages thousands of residential IP addresses across more than 190 countries, primarily through a network of users unknowingly sharing their IPs or through servers mimicking residential IPs. Most IPs rotate frequently, improving anonymity and reducing the chance of IP bans on target sites.
Connection Setup
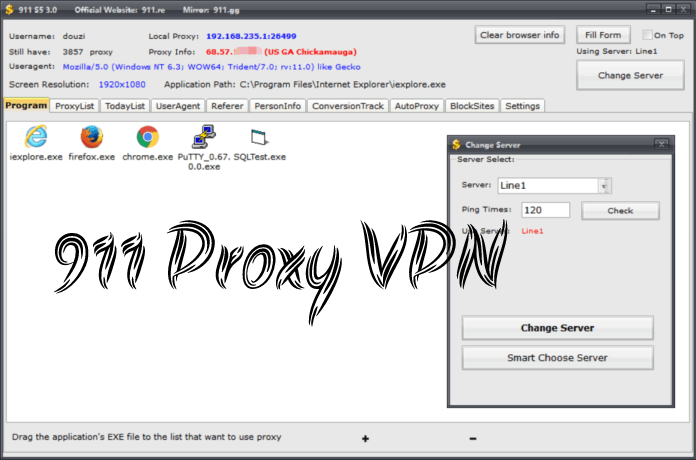
Users install specialized client software that connects them to the proxy network. This software:
-
Routes internet requests through proxies assigned by the service.
-
Encrypts traffic similar to VPNs but focuses on IP masking using residential IPs.
-
Supports proxy protocols such as SOCKS5.
Complexities and Controversies
-
The original 911.re platform was linked to shady “pay-per-install” schemes, bundling software that converted users’ computers into proxy nodes—raising privacy and legal concerns.
-
Despite this, the network’s vast IP pool remains attractive for certain use cases demanding residential IP authenticity.
-
The service’s website and official app were compromised several times, emphasizing the risks involved.
Key Benefits of Using 911 Proxy VPN
-
Real Residential IP Addresses: Reduces blocking by services targeting data center VPN IPs.
-
High Anonymity: IP rotation and diverse geographic locations enhance stealth.
-
Bypass Geo-Restrictions: Access region-locked content using residential IPs from allowed countries.
-
Reduced IP Blacklisting: Residential IPs are less likely to be banned by websites compared to data center proxies or VPN IPs.
Major Risks and Concerns
-
Security Vulnerabilities: Original service bundled adware and potentially harmful applications.
-
Legal and Ethical Issues: Using proxy networks built on unwitting user devices raises ethical questions and could violate laws, depending on use.
-
Unreliable Network: Frequent downtime, compromised nodes, and inconsistent speeds.
-
User Privacy Risks: Some traffic could be intercepted or monitored given the service’s shady history.
-
Operational Complexity: Requires technical knowledge to set up and maintain effectively.
Safer Alternatives to 911 Proxy VPN in 2025
Modern threats and regulations necessitate safer, more transparent options:
| Alternative | Description | Use Cases | Benefits |
|---|---|---|---|
| NordVPN | Leading VPN service with extensive server network. | General secure browsing, streaming | Reliable, easy to use, audited no-logs policy |
| Bright Data Residential Proxies | Enterprise-grade residential proxy network. | Web scraping, market research | Transparent, legal use policies |
| Smartproxy | Residential and mobile proxies with rotation features | SEO monitoring, ad verification | Flexible pricing and compliance |
| ExpressVPN | Fast VPN with strong encryption and privacy focus | Privacy, bypass geo-blocks | User-friendly, high speeds |
How Cybersecurity Professionals Use 911 Proxy VPN
Security researchers and penetration testers may leverage 911 proxy VPN for:
-
Simulating attacks or testing web applications with geographically dispersed IPs.
-
Bypassing IP-based restrictions during threat analysis.
-
Gathering threat intelligence while maintaining anonymity.
However, professionals are advised to weigh risks carefully and prefer vetted, compliant proxy services.
Setting Up and Using 911 Proxy VPN Safely
For those determined to use 911 proxy VPN, here are critical safety tips:
-
Obtain software only from trusted mirror sites to reduce malware risk.
-
Use sandbox or virtual machine environments to contain potential threats.
-
Regularly update security software to detect malicious activity.
-
Avoid transmitting sensitive data over untrusted proxy networks.
-
Use in combination with reputable VPNs to add encryption layers.
Frequently Asked Questions (FAQ)
1. What is 911 proxy VPN exactly?
It is a proxy service that routes traffic through residential IP addresses worldwide, often combined with VPN features for added privacy.
2. Is 911 proxy VPN safe to use?
Due to its history of bundling adware and compromised software, it carries risks. Caution is advised, and safer alternatives are usually recommended.
3. What are common uses of 911 proxy VPN?
Used for anonymity, bypassing geo-blocks, web scraping, ad verification, and security research.
4. Can 911 proxy VPN guarantee anonymity?
No technology guarantees absolute anonymity; 911 proxy VPN offers some IP obfuscation but may reveal user info if misused.
5. How do 911 proxy VPN and traditional VPNs differ?
Traditional VPNs route all traffic through secure tunnels owned or contracted by providers. 911 proxy VPN routes through third-party residential IPs, sometimes without users’ full knowledge.
6. What are reliable alternatives to 911 proxy VPN?
Top commercial VPNs like NordVPN, ExpressVPN, and enterprise proxy providers like Bright Data offer more secure, compliant options.
7. Can businesses legally use 911 proxy VPN?
Businesses should consult legal counsel; the service’s opaque origins and risks generally make it unsuitable for corporate compliance.
8. How popular is 911 proxy VPN in 2025?
Despite risks and shutdown rumors, some clone or mirror services attract privacy enthusiasts and proxy users worldwide.
Conclusion and Call to Action
911 proxy VPN presents an intriguing but controversial tool in the privacy ecosystem, offering access to vast pools of residential IPs with mixed safety and ethical implications. For cybersecurity professionals and industry leaders prioritizing secure, compliant, and transparent operations, relying on reputable VPN and proxy providers is paramount.
Evaluate your privacy and operational needs carefully, and invest in trusted solutions offering robust security and reliable performance. Empower your digital footprint with smarter, safer anonymization tools for 2025 and beyond.
Would you like an extended guide on deploying proxies and VPNs securely or a review of the top enterprise privacy tools next?