Cisco updated the security notices of three vulnerabilities patched early in August to warn customers that its PSIRT team knows that public exploit code is available.
Of the three flaws in the Cisco 220 Series Smart Switches Small Business Series, two are critical remote code execution (CVE-2019-1913) and safety bypass authentication (CVE-2019-1912).
A remote attacker who is not authenticated might use it to execute arbitrary root code and upload arbitrary files, respectively.
The third vulnerability is the CVE-2019-1914 command injection vulnerability which could potentially enable authenticated remote attackers to start a command injection attack.
As explained by updated Cisco security advisories:
The Cisco Product Security Incident Response Team (PSIRT) is aware of the existence of public exploit code. Cisco PSIRT is not aware of malicious use of the vulnerability that is described in this advisory.
All three were reported through the VDOO Disclosure Program of the Company by the same security investigator, known as the’ bashis.’
The company also patched over 30 critical, high-gravity faults found in its Integrated Management Controller (IMC) and Cisco Unified Computing System (UCS) software.
Of these, 15 have high safety flaws, while four have been considered critical with baseline values of CVSS v3.0 of 9.8. Three of the latter are bypass authentication defects, while the last is a default vulnerability to credentials.
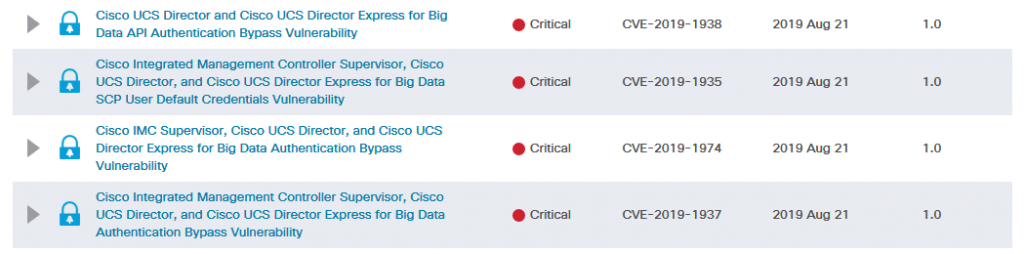
These are the details of Cisco’s security advisories for four critical flaws:
• CVE-2019-1938, a vulnerability in the web-based management interface of Cisco UCS Director and Cisco UCS Director Express for Big Data
• CVE-2019-1974, a vulnerability in the web-based management interface of Cisco Integrated Management Controller (IMC) Supervisor, Cisco UCS Director, and Cisco UCS Director Express for Big Data
• CVE-2019-1937, a vulnerability in the web-based management interface of Cisco Integrated Management Controller (IMC) Supervisor, Cisco UCS Director, and Cisco UCS Director Express for Big Data
• CVE-2019-1935, vulnerability in Cisco Integrated Management Controller (IMC) Supervisor, Cisco UCS Director, and Cisco UCS Director Express for Big Data
These critical security issues enable unauthenticated remote attackers to launch low-complexity attacks after successfully exploiting devices using specially crafted malicious requests as well as using default log-in credentials.
Cisco repaired critical flaws Four critical flaws have been patched and customers are recommended to mitigate possible attacks by installing the following software releases:
• Cisco Integrated Management Controller Supervisor releases 2.2.1.0 and later
• Cisco UCS Director releases 6.7.2.0 and later (recommended: 6.7.3.0)
• Cisco UCS Director Express for Big Data releases 3.7.2.0 and later (recommended: 3.7.3.0)
Fortunately, Cisco’s PSIRT says it has not yet been aware of the malicious use of exploit code or public advertisements to address those critical vulnerabilities patched on Wednesday.











Leave a Reply