Google updated the Chrome web browser release announcement 72.0.3626.121 with a warning that the 0day patch in the release is being actively exploited wilderness.
After initially publishing the 72.0.3626.121 update on March 1 without mentioning the security flaw being abused, the Chrome team modified the announcement with vulnerability exploitation information stating that “Google is aware of reports that there is an exploit for CVE-2019-5786 in the wild.”
Security issue tracked as CVE-2019-5786 and rated as high severity by the Google Chrome team. Potential attackers can use malicious web pages to permit the previously released memory on a visitor’s computer to execute arbitrary code and to take over the device or trigger a negative service situation through their Chrome FileReader API.
Google Chrome 72.0.3626.121 While potential exploitation of a vulnerable Chrome installation may result in severe consequences from data deletion and malware infections, it is also important to understand that attackers will only be able to run code in the user browser context. This would have less impact on users who have logged onto limited rights accounts, because the attackers have fewer and more limited tools available to abuse the machine they have successfully compromised.
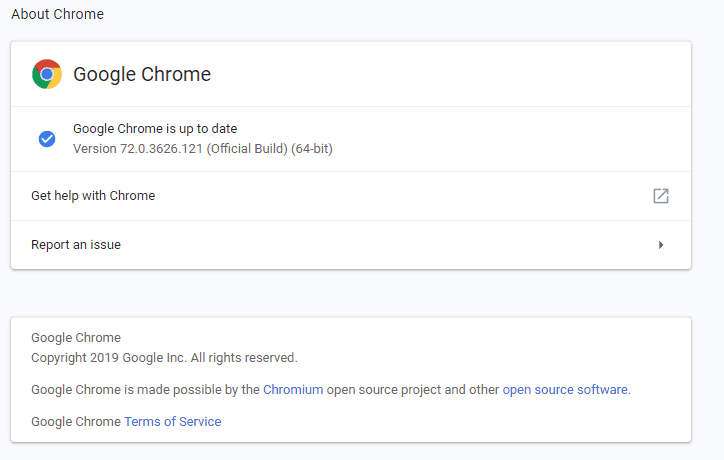
Anyway, the day’s word is “update.” Update your Google Chrome Web browser to the latest version of 72.0.3626.121, as all previous versions are vulnerable to attacks that exploit the vulnerability of CVE-2019-5786. Damage control and prevention Fortunately, Google Chrome should be configured to auto-update to the latest stable release by default, so most users need only restart their web browsers to protect themselves.
To limit any zero-day vulnerabilities, such as the just patched Chrome FileReader free use, if successfully exploited, users should always keep their apps up to date, run the software, or log into a limited account, and think about untrusted links twice before visiting websites.











Leave a Reply