A significant leak in Facebook data has been uncovered by the security research team, led by Anurag Sen at Safety Detectives. An Elastic server has identified as much as 3 gigabytes of scraped Facebook user data, which poses new questions about the company’s security measures.
It is attributed not only to the March 2018 Cambridge Analytica fiasco, but to a previous Facebook app data scraping by hackers allegedly based in Vietnam in January 2020. The data our work has uncovered is on top of what has already been uncovered, and adds 12 million more records to the list. Many of the entries, but not all, included full details of Personally Identifying Information ( PII), coming from multiple sources – including Facebook. We also do not know who is actually responsible for this scrape and how this comprehensive and invasive action could be carried out.
The server has subsequently been taken offline since it discovered the leak.
Which is Data Scraping ?
The scraping of data is a method of collecting private information from a website. It’s a relatively common practice, with many vendors providing tools that allow anyone to scrape data.
Most of the scraping of data is entirely innocent and is performed by web developers , business intelligence researchers, honest businesses like travel booker sites, as well as online for market analysis purposes. This is only when the procedure is trained and performed with a clear intention of obtaining personal information that it may have detrimental effects.
Social media companies such as Facebook will allow users to use their existing Facebook login information to access third party websites. Nonetheless, if security protocols are not properly implemented, it can allow the extraction of private information by hackers with so-called ‘scraper bots.’
Why is Data Scraping dangerous?
When private information is extracted – such as login details, addresses, and birth information – it can enable unauthorized users to commit heinous actions, including identity theft and financial fraud.
Since these leaks are mostly automated with bots doing all of the data extraction, this can mean millions of innocent users will have their information leaked in a short time. It should be noted that Facebook currently has around 2.2 billion users per month.
Then data can be sold or supplied to other malicious parties making the potential ramifications of data scraping wide-ranging and serious.
What got leaked?
The Elastic server provided data relating to 12 million Facebook users, leaking as many as 3 gigabytes.
![]()
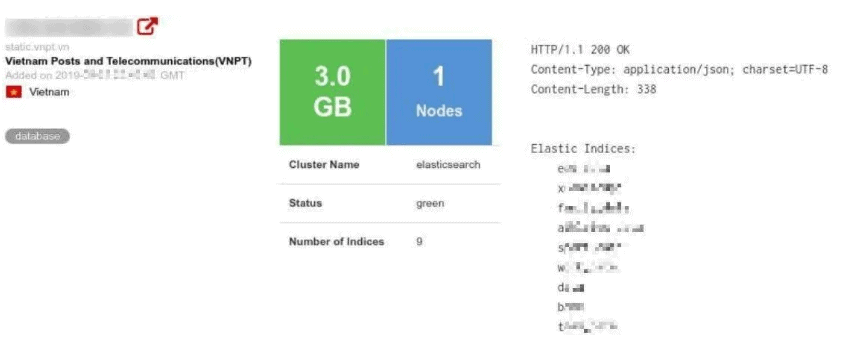
Number of Records Leaked: 12 million Facebook users
Size: 3 gigabytes
Location: Vietnam
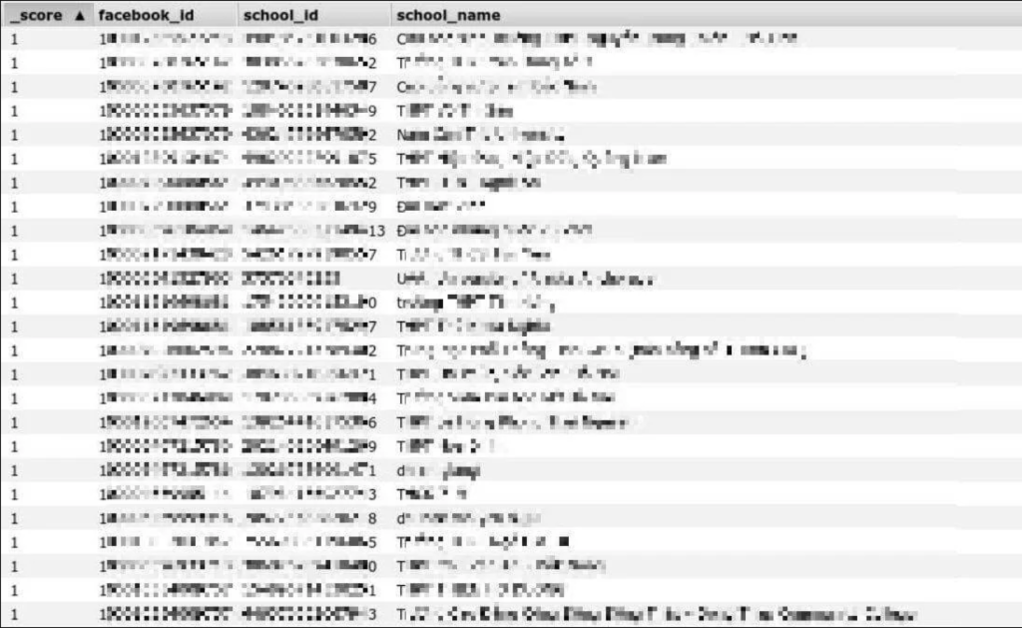
Of the scrapped and leaked data , it is important to note that much of the included information is not intended to be publicly visible , especially without user’s knowledge and approval.
Data in the breach included:
- Full name
- Hometown location
- Current location
- Education details
- Family relations with other Facebook users
- Birthdates
- GPS coordinates
- Email addresses
- Facebook usernames and IDs
- Profile scores
Possible Consequences
- Robbing personality.
- Targeted Individual Crimes.
- Blackmail and racketeering.
- Marketing not needed.
- Potential takeover of account (including enough information to reveal username and password recovery information).
Questions on Facebook
Due to Facebook’s recent experience of data scraping, this new breach in Vietnam is especially vulnerable. An older leak of data from Vietnamese Facebook users was detected at the beginning of the year, and this revelation shows that the magnitude of the threat to said data goes much further than anticipated. In March 2018, Cambridge Analytica, a political consulting group, was able to ‘harvest’ – or scrape – personal data related to 57 million Facebook users. The number of people affected was subsequently updated to 87 million, Facebook announcing that fixing the vulnerabilities would be a “multi-year process”
Because of the political connections, the incident made headlines worldwide and suspected impact on US elections. In addition , Facebook has agreed to lock down some of its API features, including data scraping, to make it harder to perform this activity. Additionally, the U.S. social media giant blocked people from using its reverse search tool — a way to use data samples to find and access even larger data sets.
It was this function that allowed malicious actors to steal user data from Facebook and the social media giant said it had been resolved.
Clearly there are still data-scraping vulnerabilities that can be exploited, particularly where the security protocols being implemented by third-party websites and Facebook are not matched.![]()











Leave a Reply