Hosting provider Hostinger today announced that after a latest safety violation that allows unauthorized access to a customer database it resets login passwords of 14 million of its clients.
The event took place on 23 August and third parties were able to access usernames, hashed passwords, emails, first names and IP addresses.
Unauthorized access to the server
More details about the incident were provided today by Hostinger in a blog post stating that a non-authorized party had access to one of its servers and had access to client data.
This was feasible because the server has an approval token which allows the RESTful API for clients and their account queries including phone numbers, home address or company address to be accessed or enhanced by privileges.
“The API database, which includes our Client usernames, emails, hashed passwords, first names and IP addresses have been accessed by an unauthorized third party. The respective database table that holds client data, has information about 14 million Hostinger users.”
Password reset action is a safeguard measure and the notice and information of how to get back on your account were obtained by Hostinger customers.
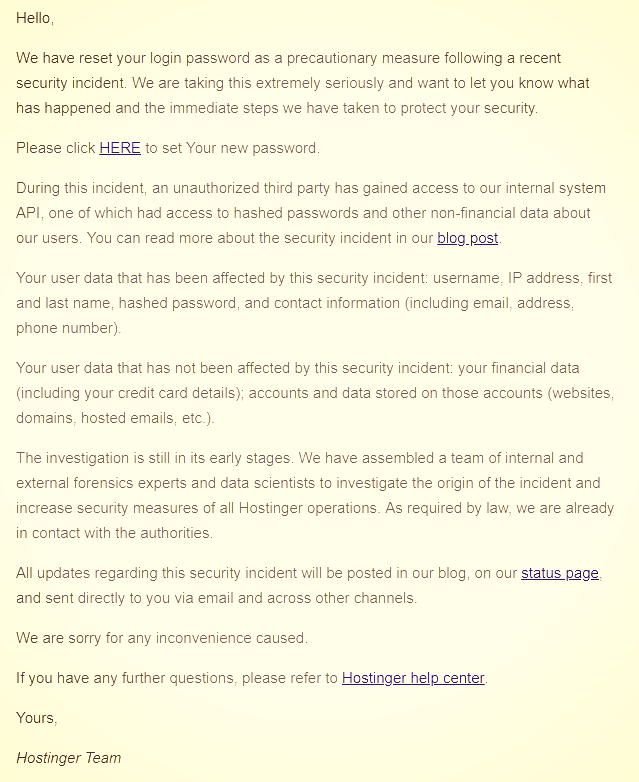
The firm claims that financial information and websites were not affected in any manner. Payment for Hostinger Services is made via a third-party supplier and an inner inquiry has discovered that information on websites, domains and hosting emails remained “intact and not affected.”
Set unique passwords
Password hashing is a useful way to stop intruders from receiving sensitive data in a clear text. However, Hostinger customers ‘ passwords may still be in danger as the business uses the SHA1 algorithm for scrambling.
An impacted Hostinger client approached the business to ask about the algorithm used to scramble passwords. The answer was that the information was hashed with SHA-1 and that now the reset passwords use SHA-2.

SHA-1 has been in use for a long time than SHA-2 and it is possible to use comprehensive databases with trillions of hacks and their initial input (rainbow tables).
Attackers use passwords acquired in credential stuffing, try accounts for different other facilities, and hope that the victim reused them.
The Secure Hash Algorithm (SHA) features are fast and can quickly be calculated in a crack attack offline. A slower version, like bcrypt, is considered more appropriate for hacking passwords.
Hostinger warns that incidents such as phishing campaigns for login details, private data or for directing to malicious websites could be exploited.
Strong passwords, which are unique to each online service, are a powerful recommendation. Both password executives can safely produce and store them.
This incident is being investigated and the violation is being looked at by a team of inner and external forensic specialists. Authorities were also approached and customers were notified.
Hostinger intends to add a two-factor authentication (2FA) safety feature in the near future. This would guarantee that the username and password alone are insufficient to access an account.











Leave a Reply