Mozilla and the Tor project are exploring Tor’s private browsing features in the shape of a privileged extension to the Firefox web browser in the early stages.
This follows an earlier expressed intent to include some Tor capabilities in Firefox in Super Private Browsing mode in the form of a May report from the Mozilla Public Research Grants 2019H1. The results of the Mozilla Research Grants were published as a research grant to examine “mozilla” for the first half of 2019. Check for mozilla vulnerability scanner here.
Both the Tor Project and Mozilla will have an insight into the potential performance issues which may be causing Tor’s integration into the Firefox browser.
Some of the problems presented in Mozilla’s Research Grants 2019H1 report, namely, the possibility of Tor integration within Firefox as part of Super Private Browsing (SPB) mode:
What alternative protocol architectures and route selection protocols would offer acceptable gains in Tor performance? And would they preserve Tor properties? Is it truly possible to deploy Tor at scale? And what would the full integration of Tor and Firefox look like?
Super Private Browsing mode became a privileged addition to it
The Tor Project followed with its call for Mozilla’s applications to the research community to send them, stating that Tor’s network performance was the most necessary consideration, which is “one of the biggest obstacles to its adoption.”
Thanks to the complexity of directly integrating Tor with Firefox, Mozilla and the Tor team are looking into using a privileged extension to measure its performance before it’s embedded into your browser.
So described in the meeting notes is the Tor mode add-on proposal:
There is an idea to, in the future, have Firefox use Tor in private browsing mode, or an a new extra-private mode. That will take a lot of engineering work and buy-in. To help smooth the path, there is a proposal for a “Tor mode” addon.
This would not be packaged with the browser by default, but would be something that users could download from addons.mozilla.org to give them a “Tor mode” button or similar.
It would allow users to experience what an eventual full integration with Tor could look like. It could also help gauge interest by counting downloads, etc. [emphasis added]
In addition, the Tor mode extension is described as ‘ a high-privileged [ …. ] addition compared with a standard WebExtension. ‘ “The add-on would configure a browser to be used as a proxy, set various prefabricated options, like that set by the Tor Browser to prevent proxy circumvention and fingerprinting. ‘
“Discussion of visual options for UI. Clicking the Tor-mode button would probably open a new window that uses a dedicated profile. This is because some of the prefs that the addon has to set are global to a profile, not to a window or a tab.”
In addition, since unauthenticated HTTP traffic through tor exit nodes may be dangerous and NoScript does not enhance the user experience, it is “easiest to apply (require) the HTTPS in Tor mode.”
Tor Browser patch uplifting on hold
The Tor Project told BleepingComputer that they are “in the early stages of exploring this with Mozilla. Tor has never been deployed on this scale, so both the Tor Project and Mozilla are investigating considerations to see if integration is possible.
“Also, Senior Director Selena Deckelmann of Firefox Browser Engineering told that “the discussions during the Tor gathering included considerations for integration.”
Example Tor features added to the Tor Uplift project
While the designers of Mozilla have already began to include some Tor characteristics in Firefox as part of the Tor Uplift project intended to “land all Tor Browser patches so that Tor can immediately use Firefox primary trunk instead of a fork,” patch uplifting will be paused for at least a few months according to the Tor conference notes.
Tor Browser features included in Firefox
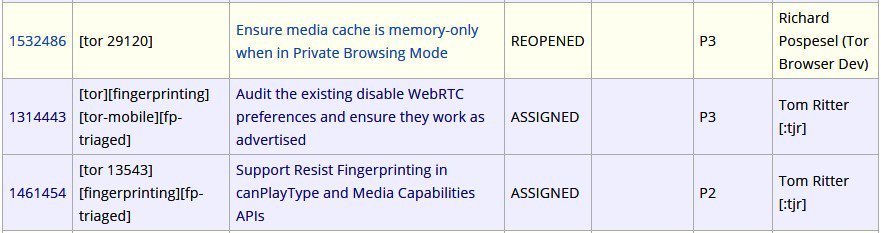
A color-coded list of Tor Browser ticket patches is presently accessible HERE for upgrading to the Firefox codebase.
Over the years after efforts to fingerprint their users, Tor Browser characteristics included in Firefox Mozilla have already incorporated several Tor Browser protection characteristics into Firefox.
For instance, Mozilla engineers included a new mechanism with the release of Firefox 52 in December 2016 that automatically blocks websites from fingerprinting users using system fonts.
Mozilla also borrowed another Tor Browser function that enabled Firefox to avoid user fingerprinting efforts through the October 2017 HTML5 canvas element.
Mozilla is not the first person to consider using Tor to improve the privacy of Firefox users, since Brave already has Tor anonymity software open-source in private browsing mode.
This enables Brave consumers to hide their browsing behaviors from employers and Internet Service Providers and to hide the IP addresses of their websites.
The newly gained Tor features of Brave enable its users to avoid monitoring while browsing the internet and protecting their privacy without installing any extra software on their pcs.
As the Tor Project also informed, “Integrating Tor into Firefox would bring true private browsing and a more secure Internet experience to a worldwide never-ending group of individuals, so we’re excited to explore this option.”











Leave a Reply