The DNSpionage Malware campaign added a new stage of recognition to show that the attackers are cleverer with their objectives and a new. NET malware, known as Karkoff, designed to enable them to remotely execute codes on compromised hosts.
The new victim survey phase of DNSpionage will also enable it to be avoided by researchers and to put its malware payload on sandboxes designed for malware analysis, as the security researchers Warren Mercer and Paul Rascagneres Cisco Talos have explained.
As Cisco Talos revealed in November, the DNSpionage attack campaign uses a custom remote management tool, enabling communication with its control servers (C2) via HTTP and DNS channels and also providing the malware campaign.
The hacking Group also uses the Mimikatz credential dumper, several Off-Shop management tools, the Bitvise WinSSH SSH server, a number of open source hacking tools, and SSH tunneling program in the same network, along with French CERT-OPMD security scientists, which also provide the ATT&CK matrix mapping for campaign users. Start using free ssh vulnerability scanner online to prevent from hacker.
New malicious tools for improving attack efficiency
Since the initial report, DNSpionage hackers have been improving their attack methods and expanding their malicious toolkit, as Cisco Talos learned in February when new and upgraded malware was discovered during the attacks.
Furthermore, in the new recognition phase added to the campaign, “the malware drops a Windows batch file (a.ba) to run a WMI command and get the entire running process on the victim’s machine.” In conjunction with the NetWkstaGetInfo) (API request, it collects workstation information that is designed for the victim’s fingerprinting system.
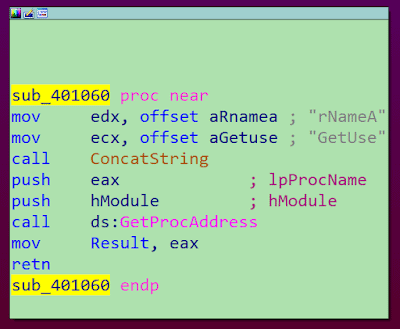
Split API call
The attackers also improved the ability of the malware to hide its activity by splitting API calls effectively violating Yara’s rules to detect malicious activity based on specific strings.
DNSpionage will also verify whether the Avira and Avast malware solutions have been installed on compromised computers and will adapt their actions accordingly, disregarding some of their configuration options.
The researchers subsequently stumbled upon a new.NET-based malware distributed through DNSpionage campaign which, after one of the inner text names they discovered, they named “Karkoff.”
The malware is very lightweight compared with other malware due to the small size of it and allows remote code execution from the C2 server,” says Cisco Talos.
What makes Karkoff somewhat’ special’ is that it logs all the commands it executes in the affected systems — and it also attaches time marks to each and every one of them— making it much easier for its victims to identify damage.
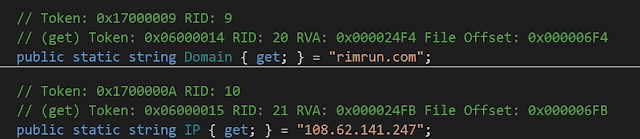
After realizing that the infrastructure overlap, Cisco Talos has been able to link Karkoff’s new malware with the DNSpionage campaign, both using rimrun[.]com as a C2 server, with IP addresses previously used by the malware attacker in relation to their malware campaign.
DNS hijacking alert from the DHS
Domain Name System (DNS) is a service that enables users to enter domain names in Web addresses rather than enter them in the Web servers IP addresses in their web browsers.
Access to DNS records through DNS hijacking attacks enables actors at risk to redirect the name servers of their targets towards their own infrastructure, allow their victims to funnel to servers they control and jeopardize them through malware or various malicious tools.
As discovered by Cisco Talos, during the initial phase of the attack, the DNSpionage attackers set their sights on different Middle East targets and launched attacks by DNS hijacking on several Lebanese and United Arab Emirates areas of government.
DNSpionage C2 Hardcoded Servers
At the beginning of this year after the DNS hijacks reported by the Cisco Talos Group, FireEye, and CrowdStrike, the Homeland Security Department (DHS) issued a DNS hijacking campaign warning requiring all US agencies to verify whether the.gov or agency-run domains are addressed with the right IP addresses.
Moreover, only last week the team of Cisco Talos also revealed the details of the state-sponsored attack campaign ‘ Sea Turtle’ which used DNS hijacking to compromise some 40 public and private organizations in 13 countries.











Leave a Reply