The Mac malware developers called ThiefQuest continue to improve their development and researchers have found that the latest versions of the threat no longer have ransomware functionality.
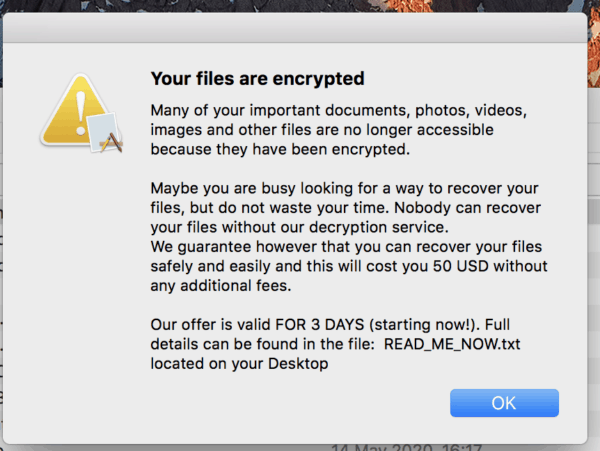
ThiefQuest (aka EvilQuest) first discovered at the end of June initially appeared to be a piece of ransomware but a detailed analysis revealed that it also allowed its operators to steal data and take full control of an infected device. In fact, security experts found that the ransomware functionality was incomplete and the main aim of the malware was possibly not to help threatening actors make a profit from the victims’ ransom paid.
It seems that the hackers didn’t actually intend to retrieve encrypted files, but they also didn’t put too much work into ensuring encrypted files couldn’t be retrieved, enabling SentinelOne to build a tool that allows victims to restore files.
While its ransomware capabilities may not stand out, ThiefQuest allows its operators to steal various types of information, including images , documents, databases, source code, cryptocurrency wallets and encryption keys.
Trend Micro researchers have analyzed many samples of Mac malware and found that it continues to make changes and improvements for its developers.
We found that the new ThiefQuest versions do not include the features of file encryption and the malware does not drop a ransom note any more. Ironically, the initial versions, first appearing in early June, focused on providing backdoor capabilities and ransomware technology was introduced only in the second and third generations. However, ransomware capabilities are no longer included in the fourth generation which emerged in early July.
Trend Micro researchers, on the other hand, noticed new functionality that allows the malware to run images and sound files using the default macOS software. This could indicate that the developers of ThiefQuest may be planning to reintroduce ransomware features as previous threat variants showed the ransom note in a modal window and used the speech feature in macOS to read it out to the user. In the future the new features might be used for similar purposes.
Certain noteworthy improvements found by Trend Micro in more recent versions relate to the reading of payload, compression and decompression, the generation of IP addresses for the C&C server, and improvements in file names and subdomain names of the application.
The threat actor has also made some changes to the software designed to assess whether the malware is operating in an analytical environment that would prevent researchers from investigating ThiefQuest, and the malware is now testing the compromised network for the existence of multiple security items, and attempting to stop them whether detected.










Leave a Reply