Dark Web browsers are the most important concerns for anonymous browsings, and browsers are the most widely used applications in any device in the recent times but not all browsing history is kept privately.
Unlike Dark Web browsers, other browsers With cookies, custom ads, and browsing history being tracked, people tend to lose their privacy and not everyone wants to reveal their search history to third parties regarding what they want. Google and Facebook have done this in the past, for whom their privacy violations are now being questioned.
That said, the dark web browser is helpful for people who prefer anonymity over the internet. Deep Web exists parallel to surface web but does not index the sites inside the surface unlike Google or other search engines.
What is a Dark Web?
The actual search results showing websites, blogs, videos, images, applications, software and more are only 4% of the total web database and 96% is available in the dark web. It is not only the Deeb web search engines but also public agencies that find it hard to track browsing history in the dark.
Although Dark Internet access gives the users anonymity and privacy, it also creates chaos for the government, as a lot of illegal and underworld cyber activities are part of this, maybe that’s why the Dark Web is still regarded as unethical and creepy. But, in contrast, it is very legal to access the dark web via Dark web browser Tor.
Unlike us imagine, the Dark Web that can be accessed by Dark Web browser consists not just of all illegal activity but also of the sharing of data without any restrictions by doctors, engineers, scientists, and professors.
And, as not all countries appreciate freedom of expression, the dark web helps individual people from certain countries unidentified explore and express ideas.
Some advantages and disadvantages are present about the use of the dark web,
Advantages
- Anonymity
- Freedom of speech
- Data privacy
- Knowledge
- Political activism
Disadvantages
- Illegal transactions
- Illegal trading
- Anti-government movements
Since not all browsers are compatible with the usual World Wide Web, outside of the Web surface, we need personalized or special browsing procedures with a unique set of Dark web browsers that penetrate this confidentiality space that can be carried out using Dark Web Browsers. In this article, we’ll look at the top 5 dark web browsers to keep your browsing anonymous.
This dark web browser helps you mask your identity and prevents other entities to track your IP address.
Top 5 best dark web browsers
Tor Browser:

Tor is the first dark browser on the market to be launched with absolute safety and anonymity in front of any other browser. Its exceptional power to browse in depth gave it all the credits until 2014 when the FBI hacked it. However, after this hack, Tor has fixed its gaps, making it stronger and more secure for dark web users.
However, Tor’s framework isn’t secure because it simply routes your traffic via several nodes rather than directly connecting your physical device, so it helps to limit tracking, but does not mask your IP address, and offers many more future prospects when compared to another dark web browser.
To do the same, a VPN with the Tor would be necessary to be completely anonymous. Tor is managed by a group of volunteers who use a number of relays to take care of the surge in network traffic.
In Mac OS, Windows and Linux, Tor is fully operational.
Website: https://www.torproject.org/ Setting up Tor: https://2019.www.torproject.org/docs/documentation.html.en
I2P- Invisible Internet Project
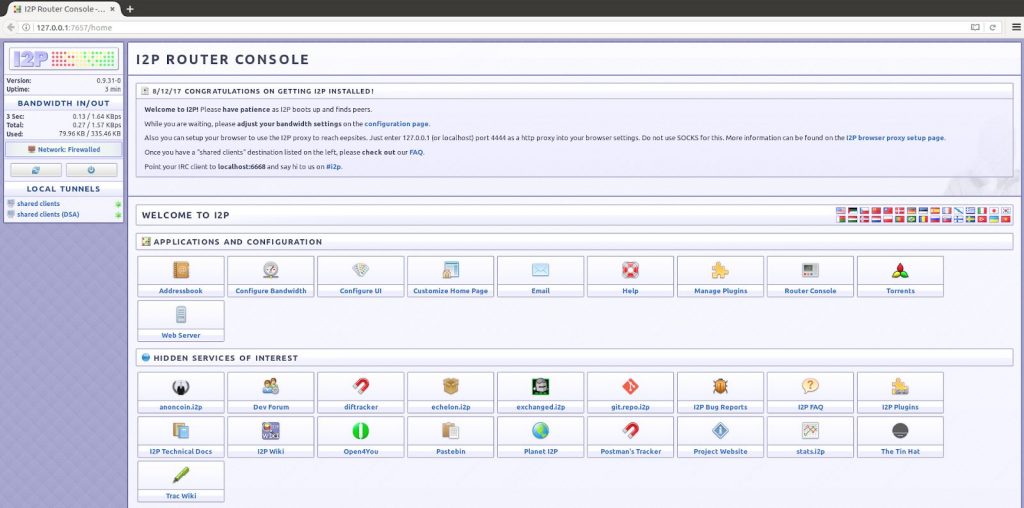
Another Dark Web browser I2P differs from Tor, since it provides anonymity when it works with multiple data streaming layers to protect your privacy.
This is strictly a message for reliable communications based on the library. Communications are encrypted from end to end (four layers of encryption) with the receiving end of cryptographic identifiers that can then be decoded with public or private keys.
The Dark web browser framework is based on a protocol for the transfer of the TCP / UDP or IP data. However, Tor structure is not secured since all it does is re-route the traffic from several nodes rather than connect your physical device directly, so tracking can be restricted but your IP address will not be masked.
I2P is built on a tunneling system where the sender creates the outbound data tunnel, the recipient has already set up a tunnel for the input data, so that the sender customer will send his message to the other customer using the inbound tunnel through this outbound tunnel and vice versa.
These tunnels are identified by requiring the same through a network base based on the kademelia algorithm, a more structured, distributed hash table. Using a standard web server, I2P is currently being used to create an anonymous site and link it to the I2PTunnel server.
If you are looking for anonymity through the web and are not prepared to create a VPN, then I2P is for you. This is another best web browser to keep anonymous.
Website: https://geti2p.net/en/
Setting up I2P: https://geti2p.net/en/about/media
Subgraph OS
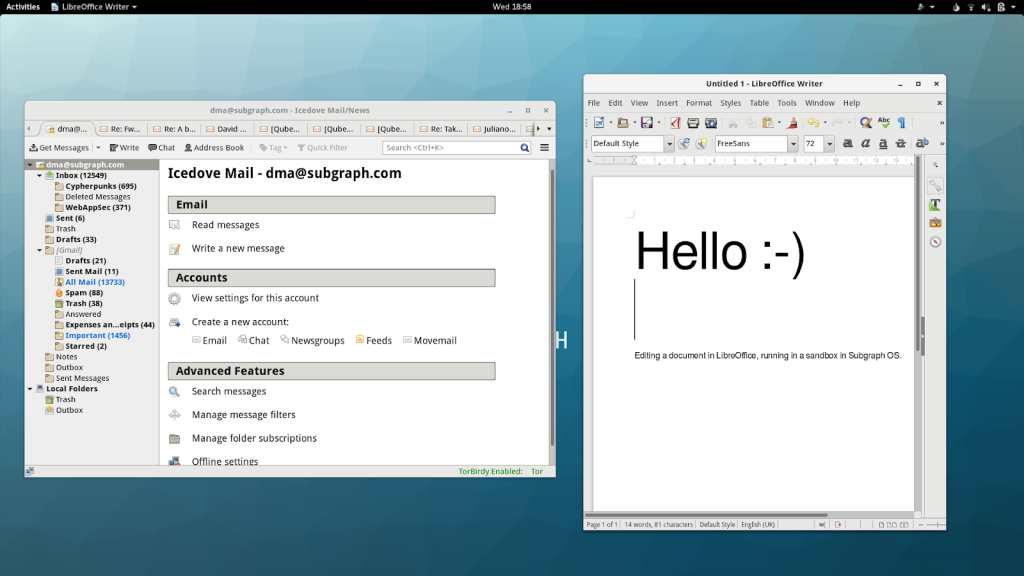
Subgraph is an open source dark Tor-based web browser. Subgraph OS is OS and not a stand-alone browser, unlike Tor or I2P. Subgraph OS uses hardness, metaproxy, sandboxing, security package, network application policies, binary integrity, and file system encryption to build robust network security.
It can isolate your navigation experience with sandboxing, remove instances where malware is detected, and separate it from the standard browsing container.
In addition to this, Subgraph also comes with a secure IM called CoyIM and an email client called Icedove to eliminate client communication vulnerabilities. Like I2P, Subgraph works on different layers, helping users to maintain their privacy and anonymity through uninterrupted access to the internet.
The Subgraph OS can always be selected as a tool for dark Web browsing with so many advanced security features.
Website: https://subgraph.com/sgos/index.en.html
Subgraph OS handbook: https://subgraph.com/sgos-handbook/sgos_handbook.shtml
TAILS
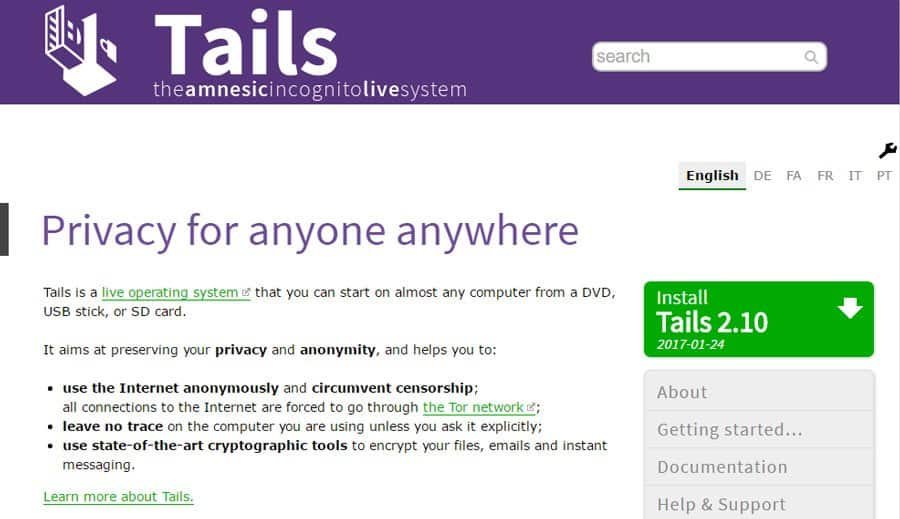
Similar to other dark web browsers, TAILS also provides users with extensive browsing and supports them. The Amnestic Incognito Live (TAILS) is a live operating system designed to provide the user with full anonymity and privacy. TAILS can be used with a USB stick or DVD in any computer.
It creates absolute privacy by communicating with the network Dark Web browser Tor, by encrypting your messages, files and e-mails using encryption tools. TAILS is free software, which when used temporarily switches off your default OS and turns it on after TAILS is shut down, so it does not require storage space because most of it runs on a RAM so there are no traces. If you want a simple yet secure dark browser, TAILS must be your cake piece.
Website: https://tails.boum.org/
Setting up TAILS: https://tails.boum.org/doc/index.en.html
Whonix

Whonix is similar to Subgraph, mean that it is not an autonomous browser, but a Subgraph-like OS built on the free software of TOR. Most of the basic TOR network framework provides the users with complete privacy and anonymity.
Whonix is so powerful that even a malware with root privileges can not track the IP of users with TOR connections. Besides the fact that Whonix is an OS, it gives users full privilege to set up and use their server by being invisible. Whoonix is supplied with pre-installed applications that can also be an additional benefit to choose from.
Besides the above advantages, Whonix comes with the’ Data Stream Isolation’ system, and it is one of the best dak web browsers available because it does not use the same TOR exit nodes.
Website: https://www.whonix.org/
Setting up Whonix: https://www.whonix.org/wiki/Documentation
Since the TOR network’s most dark web browser relay, the TOR browser is the ultimate choice for deeper browsing. However, you may check for other obscure web browsers listed above if you are looking for other features, like sandboxing, encryption of files, secure IM and e-mail clients.
Conclusion:
Because most of the dark web browser relay is located on the TOR Network, TOR is the ultimate choice for deep browsing. But you can also check other functionalities like sandboxing, file encryption, secured IM customer and e-mail customers to find other dark web browsers listed above.











Leave a Reply